Due to a serious coding mistake in the kernel stage script at Qualcomm, makers of the Snapdragon chipset, hackers can easily get root access and take complete control of your phone. As soon as the attacker(s) gets the administrator level functionality, the hackers are capable of doing nearly anything. For instance, once they have complete access to your smartphone, they are able to take screenshots, make a call, switch on your smartphone without your authorization, and access your personal information such as account profile details, online messages, text messages and debit card figures.
Qualcomm, the major ball player in the field of processor development, claims that their programs on a Snapdragon processor have the ability to power more than a million smart hardware devices, which includes numerous Internet of Things (IoTs). Therefore, this coding mistake is a subject of serious priority, especially once you consider the large number of people it will affect.
However, at the same time, the tech giant Google, and particularly the Android supplier, has rolled out upgrades following this problem of remote root accessibility. By employing this exclusively developed software update, the programmer will not be in a position to acquire core accessibility to the hardware.

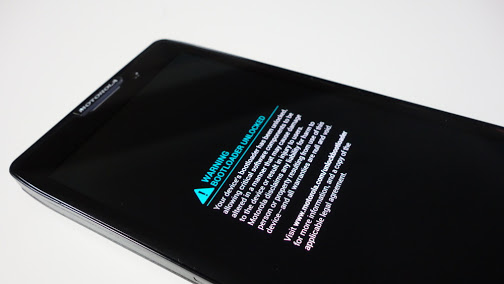
Google has already supplied patches for a few phones out there; however, the main concern is getting this security feature to other smartphones running Android (phones that are running older versions of Android). Since Android is used in almost every phone nowadays, the OTA—or, to be more precise, the process of giving this update over-the-air—is going to look something like this:-
Qualcomm will fix this issue and push out a program to Google.
Google is going to get in touch with all the various suppliers of hardware production like Sony, LG, Samsung, Huawei, HTC, etc.
Once the meetings with the hardware producers are over, the Android supplier is going to give the security patch to all the suppliers.
And after that, those patches will be further modified by the companies, and thus, an OTA update is going to be available on every device that runs Android and has a Snapdragon 800 series processor placed on their motherboard.
However, as simple as these steps look, they are truly time consuming.

Wish Wu, a mobile threat response engineer at Trend Micro says: “We have discovered a vulnerability in the integrated Android Debugger that can be used to expose the contents of the device’s memory in devices running Ice Cream Sandwich to Lollipop.” So, this is a really bad situation – not just for smartphones running on Android & Snapdragon, but also for the Internet of Things.
Almost all of Google’s flagship phones are among the devices that are affected (Nexus 5X, Nexus 6P, Nexus 6, Nexus 5, Nexus 4, Nexus 7, Nexus 9, and Nexus 10). In addition, every single smart unit making use of the Qualcomm Snapdragon 800 sequence processors—such as the 800, 805 and 810—and devices that are running a – 3.10 – type kernel, are also affected. Wu says that this problem is not just on phones that are running the latest version of Android, but they can also be found in smart devices that are running KitKat.
Source: The Hacker News, Trend-Micro Labs Security Intelligence
You want to support Anonymous Independent & Investigative News? Please, follow us on Twitter: Follow @AnonymousNewsHQ
This Article (This Android Vulnerability Can Result In Your Data Being Hacked) is free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ.com.





How can a hacker turn on my phone… if it’s off?
They can’t !!!
It may be possible, depending on who you believe.
“The baseband could be programmed so, while the power source is connected, it stays in a ready mode,” he said. “That seems to be at least a plausible assumption based on, and only based on, a number of other articles citing FBI and CIA and the agencies that have been able to locate these devices while they’re turned off.”
they have had the technology to hack phones, turn the mic on and off, the camera on and off, and even the phone itself on and off, so why the surprised reaction? technology was brought into our lives by the government to control and track our lives, either get used to it or get rid of it
Is there anything we can do other than wait to fix the vulnerability?