
For years now, attackers and scam artists have always been trying to gain access to other people’s email accounts, and if you’re like most people, you have an email account for your online activities. You probably use your email to include social media, bank accounts, personal and business emails. Along with everything you do, you still get spam messages on a daily basis.
Whenever you first setup your email account, you may recall having to include your phone number for security purposes. With that being said, we can now look into how an attacker can gain access to your email account with your phone number.
The first step the attacker will need to do, is find their victims email and phone number. This is easier if they are your friends, or know you on a social media site such as Facebook. Once the attacker has your information, they then proceed to bypass your password.
The first step is to click on “Forgot Password.” 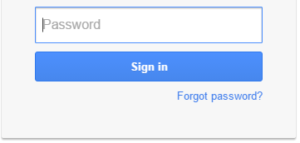
When the attacker clicks on the Forgot Password, they are then redirected to a page in which they attempt to remember their password. The “I Don’t Know” button allows the attacker to bypass this step and move onto the next part.
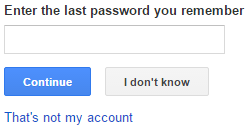
It Worked! Now the attacker can have a special code sent directly to your phone via text message or phone call. The attacker would use the text messaging services, as you can refer back to the message later on during this attack. All the attacker has to do now is click on “Receive Via: A Text Message (SMS)” and then the button “Continue.”
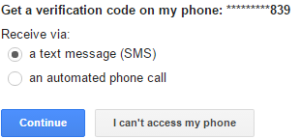
Now the attacker is looking at a screen that requires them to input the code that Google has sent.
Now that a text message from Google has been received saying “Your Google Verification code is 555555,” as you can see below.
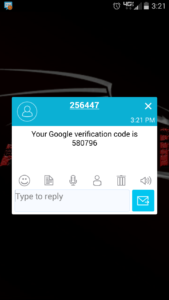
So you have a message from Google with a verification code, but the attacker doesn’t have your phone. How can they get access to that code? They then send you a fake text message that says something similar to the following:
“This is Google, we have noticed some unusual activity with your account. Please send us the code that was just sent to you and your Google Gmail account will be unlocked.”
And that is when you go back and look at the code, and send it.
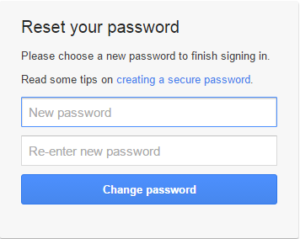
Now your attacker has the code and proceeds onto the next phase, resetting your password. At this screen, the attacker can set your email account password to anything they desire. 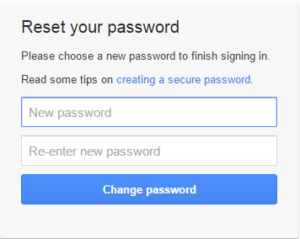
Now the attacker is in your email account. What do they do now? If you have your social media sites connected to this email, they can change those passwords by using a password reset link sent to that email, they can log into your bank account, and basically take over your life…depending upon how much you use the online services.
So how do you protect yourself from this social hack? If you get a random message with a verification code and you didn’t ask for it, you are being hacked. Simply log into your email to make sure nothing else is going on. When you get the second text message, you can either reply to it, or ignore it. If you reply then you are only provoking the situation, ignoring, and eventually they will stop sending you messages. If you do get these text messages, you can always contact your local authority and provide them with the messages and the contact numbers, so they can initiate their own investigations.
As you can see, there are more ways than one to hack email accounts.
This article (Email Hacking with Phone Number) is a free and open source. You have permission to republish this article under a Creative Commons license with attribution to the ITNinja and AnonHQ.com.





This has been known for years, I used to do it back in 2008, when I wanted to get xbox accounts. This is definitely not something new.
podrias hacer lo mismo con cuentas de facebook con este procedimiento?
Anyone who gets a text message like that and responds with the verification code deserves to be hacked. There are consequences for being stupid, and the sooner they’re meted out, the better.
So its not technically a hack. It requires the user to do something, and it depends all on the user.
the way that works now is a friend has relations at phone companies and breaks you every mail
Thank you for sharing this superb website.|
cs go skins analyst http://www.boom247.com/ads/nba-2k16-mt-coins-world-extensive-net-and-im-in-a-position
This is social engineering. Might as well just convince the slave to give you his password in the firs place, has about as much chance of working.
this has been fixed sadly