
The assistant professor at Princeton, Arvind Narayanan, who is a graduate student from Steven Englehardt has conducted a large massive study upon how exactly websites track their users by utilizing different techniques.
The results displayed on the Princeton Web Census research can show us that the massive search engine Google, through multiple domains, possesses the ability to track users.
The Serial Killer Tracker – Google!
The researchers have revealed that the Google-owned domains, in which browsers are able to load the tracking code, hold the accounts for the top 5 of the most popular trackers.
Fact: After performing the study of the top 1 million sites, the researchers also discovered that there are just over 81,000 different domains in which have also enabled the tracking code loaded to their website. As we take a closer look at this data, those researchers have also announced that there are only 123 of third-party trackers that are found just above one-percent of all websites.

This suggests that the total number of the third party trackers in which are utilized regularly, will experience this on a normal daily basis, is actually rather small. This effect is accentuated as we look into the different third-party entities in which are owned by the same entity. We also know that Facebook, Google and Twitter hold the only third-party entities that are clearly present on more than ten-percent of websites.
What does all of this mean? In essence, there is a high chance that as you visit a website, or even click on a link, that one out of three major companies, if not all of them combined, will already know about it. This holds most plausibility through Google, in which the company loads a tracking code on four out of five websites.
The third party trackers are moving to implement an audio-based fingerprinting.
In order to fully collect their data, the researchers had to utilize a special piece of software that they customized. They called their software OpenWPM, which they have generously hosted online as an open-source. The OpenWPM loads several websites inside Chrome, Firefox, and the Internet Explorer. Thus, collecting several packets of data on the tracking technology that is loaded onto each page.
This OpenWPM will search for third-party JavaScript files, Flash Objects, Cookies, Fonts, and even fingerprinting techniques. Such as the ones that utilizes the HTML5 canvas, Audio Context, and API’s as well as WebRTC local IP discovery.
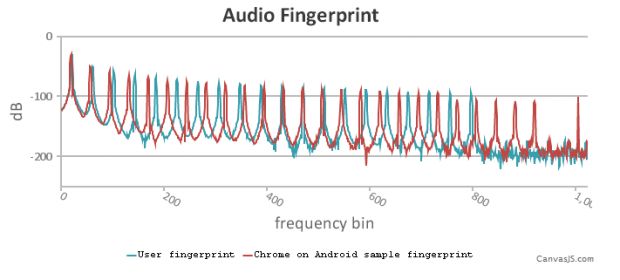
However, out of all of the third-party entities, the latest of the tracking technology family discovered, also happens to leverage the Audio-Context API. Normally other third-party tracking entities will use it in order to send a low-frequency sound to a user’s computer, to measure how the user’s computer processes the data, thus resulting in creating a unique fingerprint solely based upon the user’s hardware and other software capabilities.
If you would like to be able to check your own audio fingerprint, there is a demo page setup by the researchers for you to use.
The results from the Princeton survey are not much of a surprise to us, as we have seen similar studies carried out by researchers from MIT and Oxford. Their research was published earlier this week; it also reveals that the Twitter Location Tags, that on just a few tweets, can allow for details about a specific accounts owner to be examined closely: their real-world address, their hobbies, and even medical history. However, this data was collected by Twitter, who is using it to deliver more advertising to specific targets.
However, tracking entities are not just found on the World Wide Web. Other recent studies, such as the one by the researchers from Stanford, has shown that a phone call, as well as phone’s metadata, can be utilized to study your phone details, which provides personal information about you. While your cell phone carrier is not listening to your phone calls, they may know just as much about you as Google does, if not even more.
![]()
The studies performed have also revealed that it is clearly becoming more difficult to maintain a low profile while carrying out your personal life online, or even on your phone. Some known users will block the HTML5 canvas fingerprinting, however, they may also use their cell phones on a more regular basis. For those who do not use mobile phones, then the WebRTC will reveal their real IP address, even if they are hiding behind a wall of VPN’s. However, regardless of how different users may attempt to avoid the third-party trackers, there will always be someone in the shadows watching us.
**Please download a PDF Version of this article for future offline reading HERE**
Sources: News.Softpedia, GitHub, Princeton Web Census, OpenWPM, News.MIT, PNAS.
This article (Google Knows Everything You Have Clicked on Online) is a free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ.




what about the tor browser? is it also tracked , eh?