Thursday, June 26, 2014
Written by: Anonymous Singer
As we all know we live in an unfair world with hidden dictatorships by our own governments. We have to abide by the rules and we will be liable if we do not, but when it comes to the government itself; they do not know anything about it and they never want to!
The National Security Agency (NSA) and FBI are using spyware to access a suspect’s phone for, as they claim, the purpose of surveillance. This has been found by researchers from the Citizen Lab at the Munk School of Global Affairs at the University of Toronto and computer security firmKaspersky Lab.
For what can the malware be used?
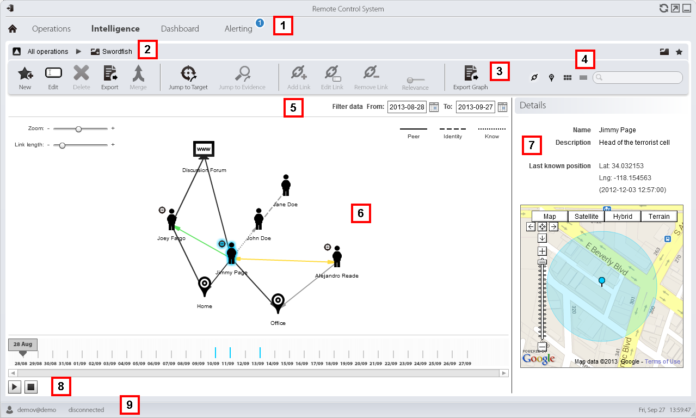
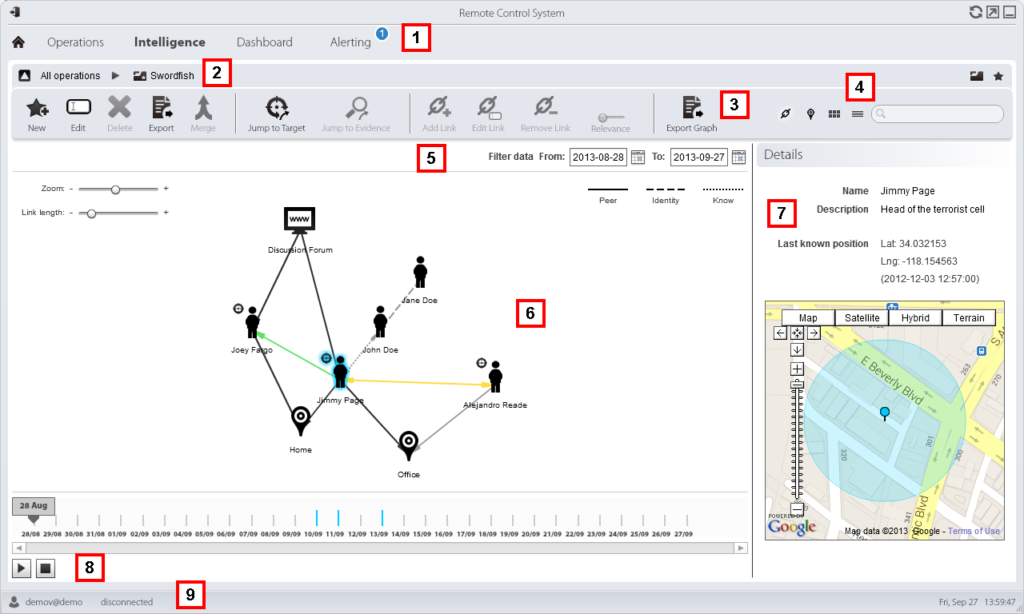
The malware named RCS, Remote Control System, is developed by an Italian IT company known as “Hacking Team”. They sell the RCS to governments and law enforcements. The RCS can already be used for desktop computers, laptops and all kinds of jailbroken and non- jailbroken Smartphones, like Apple, Android, Windows, Symbian and Blackberry. The malware installs with the help of an Evasi0n jailbreaking tool.
Both researchers have recently presented their findings during an event in London. The outcomes were astonishing; the size of the command infrastructure supporting Hacking Team is increasing very fast with already 326 command-and-control (C&C) servers running in more than 40 countries.
“It was a well-known fact for quite some time that the HackingTeam products included malware for mobile phones. However, these were rarely seen,” said Kaspersky Lab experts on the blog post. “In particular, the Android and iOS Trojans have never been identified before and represented one of the remaining blank spots in the story.”
Worldwide usage of C&C servers
Researchers of Kaspersky Lab have scanned the entire IPv4-space by using a fingerprinting method to identify the IP addresses of RCS Command & Control servers around the world and they found the biggest host in United States with 64 C&C servers. The second country in the line was Kazakhstan with 49 servers, the third was Ecuador with 35, the UK with 32 was fourth and so on. All named and other countries summed up together, gives 326 Command & Control servers.
“The presence of these servers in a given country doesn’t mean to say they are used by that particular country’s law enforcement agencies,” said Sergey Golovanov, principal security researcher at Kaspersky Lab. “However, it makes sense for the users of RCS to deploy C&Cs in locations they control – where there are minimal risks of cross-border legal issues or server seizures.“
Working process of RCS
RCS can be physically or remotely installed. Physically goes through a USB or SD Card and remotely, it is done by spear phishing, exploit kits, drive-by downloads and network traffic injection.
Once it is installed on your Apple or Android device, it allows governments and law enforcement officers with larger capabilities to monitor victim devices and gives them the ability to:
–control phone networks
–steal data from their devices
–record voicemails
–intercept SMS and MMS messages
–obtain call history
–report on their location
–use the device’s microphone in real time
–intercept voice and SMS messages sent via applications such as Skype, WhatsApp, Viber and many more.
“Secretly activating the microphone and taking regular camera shots provides constant surveillance of the target—which is much more powerful than traditional cloak and dagger operations,” Golovanov wrote.
Although the Android module is protected by DexGuard, an optimizer which makes it extremely difficult to analyze the device, most of the abilities mentioned above are also available for Android, along with the support for hijacking applications such as Facebook, Google Talk, Tencent of China and many more.
Researchers said that the mobile modules are custom-built for each target.
At last, we have concluded from previous disclosures that RCS is currently being used to spy on political dissidents, journalists, human rights advocates and opposing political figures.
What can you do to protect your Smartphone, Tablet, PC & Laptop against Spying and Hackers?
-> You can use a VPN, for more information click here or on the link below:
Surf anonymously, protect yourself from hackers and hide yourself from NSA




WTF! What kind of article is this? Tell us how to detect and remove it you dick!
You are the dick here. This guy is just stating facts for the fellow Anon to be aware of and do something about it. This is a fine article, and you’re saying it like he’s the problem. If you cant respect people just giving out facts, then you shouldn’t even be here.
PLAY NICE NOW, WE ARE ALL CONNECTED & AS THE SAYING GOES….. KINDNESS, DOESN’T COST A THING! SPRINKLE THAT SHIT EVERYWHERE! YOU MAY MAKE SOMEONES DAY BY SPREADING KINDNESS. I HEARD A FEW STORIES OF PEOPLE ACTUALLY SAVING SOMEONE FROM SUICIDE BY BEING KIND. <3
YOU DA REAL MVP! 🙂
I agree – we’re all connected to one, infinite consciousness and saving someone from suicide just through sending kindness their way is a very real event. SO people need to STOP being so mean and angry, violent, and blood thirsty all the time. This will contribute to putting an end to meaningless killing, not excluding the killing of oneself. Help stop the wars by starting with the man in the mirror, people.
Are you talking in first person Dick/Richard?
First of all, I would like to say that everyone has the right to form an opinion, but we have got to remember; even though you “could” be a suspect according to the government, it does not give them the right to treat you as a criminal already, by secretly controlling your phone and stuff. By the way, this goes far beyond breaking the rules with respect to privacy.
However, we do not defend criminals. We just try to let you people know what is going on out there based on facts and evidences. Asking for a solution? I totally understand, but do not expect from us to give immediately all kinds of solutions on every issue. If we have a solution, we will definitely publish it. Besides that, you could change your habits which could already prevent all kinds of unwanted stuff.
At last, we are fighting against the governments that try to hide their secrets behind weak arguments!
We are anonymous!
We are Legion!
We do not forgive!
We do not forget!
Expect us!
then dont use a smartphone dumbass
🙂
Suspects phone …. Definition of suspect: a person who is believed to be possibly guilty of committing a crime
: a thing that is thought of as a possible cause of something bad! If you’re not doing anything illegal why would you worry about it!
Maybe because I don’t want anyone knowing what I do with my life on a daily basis unless they’re a part of it. Maybe because I don’t like the idea of someone else arbitrarily deciding what is and is not right for me, especially with regard to personal choices that don’t hurt any other human beings in any capacity. Given the broad-spectrum abuse of citizens’ rights to privacy that the NSA and other “security agencies” have engaged in, I don’t trust them not to use this to profile and detain “potential threats” based on a political agenda, the whim of a corrupt or sadistic agent, or any of the myriad problems we see with current law enforcement in general.
Let me pose the question back to you in a different way: if you’re not doing anything illegal, why are they worrying about monitoring you?
Part of me thinks yeah why worry im not doing anythjng illegal….but no, we should Worry cause it’s invasion! Something else that’s yours that u pay for that as being robbed! Fuqing nosey bag of dicks!
you realize they are profiling anyone thats not in there political side as dissidents and potential criminals. as such you are all targets ,
My friends just stay calm i know it all seems stupid and very immature of the government for putring in these softwares in now somehow we need to find away to dind this program and some how remove it
Can anyone make this type of program of course some plp can and they should make it and publish it on apple or google play store
If your phone’s getting hot, running out of battery life, etc. New phones make it easier to hack undetected, too.
Also, it makes it seem like a game, I think that is for many who have terrorist protection. No one is above the law, that’s stupid. Law is not changed and their is a punishment for those who violate it … just wait a bit, have to be much larger than those of all states alike.
I’ve also heard from many people that the government, but i highly doubt it’s only the government, that they also hack into Xbox Kinect ect ect.
SCAREY STUFF. THIS IS SO WRONG ON SO MANY LEVELS.
Funnily enough Dick is short for Richard. How ironic.
When someone says: “If you don’t have anything to hide, you’ve got nothing to worry about” what I hear is: “I don’t care if my government treats every single citizen as guilty before proven innocent”. Basically what any government is saying by spying first before substantial prima facae evidence is presented and a warrant is secured through appropriate and legal channels is: ” You’re all criminals. You just haven’t committed your crimes yet.”
This whole thing is starting to sound more and more like Nazi Germany! Where people were considered guilty until proven innocent.
Another way to monitor everything we do in our lives. Another way to spy on us if they want to. Another way to gain personal information about everyone so it can be used against that person if they need to.
I call that Blackmailing, I call that illegal hacking.
I call that living in an invisible box that has ”freedom” written all over the invisible walls, so long as you live your life like they want you to, without you knowing of them, that invisble wall will never exist. But as soon as you start to dig harder and see through the lies and you know who is really pulling the strings, that invisible wall suddenly becomes a reality. You will find yourself living in a box that they control.
Treating us like this means that the ruling elite considers us as ”criminals”, we just haven’t commited the crime yet.
But we can fight this, we can protect ourselves, our identity so that the invisble box will vanish. We can stand up against this, but only if we stand up Together. Only if we all face the facts and realize the problem, we are being controlled and ruled by an elite few who only crave for more power and money. Only if we realize this problem, we can fight it.
Share our idea with the world, the idea of true freedom, and you are Anonymous.
We are Anonymous.
We do not forgive.
We do not forget.
Expect us.
Thank you todd and killcalibur. Was really starting to lose faith there for a few minutes.
The government is the government and able to do mostly what they want, why not just pass a law having the malware already installed in all new phones and devices.
I’m sure that will be the governments next step!
Great information however someone else already wrote this article and it’s been reposted under a new name as author
That it partly correct. This article is rewritten and there are some changes made, where needed.
Further, I would like to say that everyone has the right to form an opinion, but we have got to remember; even though you “could” be a suspect according to the government, it does not give them the right to treat you as a criminal already, by secretly controlling your phone and stuff. By the way, this goes far beyond breaking the rules with respect to privacy.
However, we do not defend criminals. We just try to let you people know what is going on out there based on facts and evidences. Asking for a solution? I totally understand, but do not expect from us to give immediately all kinds of solutions on every issue. If we have a solution, we will definitely publish it. Besides that, you could change your habits which could already prevent all kinds of unwanted stuff.
At last, we are fighting against the governments that try to hide their secrets behind weak arguments!
We are anonymous!
We are Legion!
We do not forgive!
We do not forget!
Expect us!
Easiest way to avoid this problem is to ditch the F-ing phone ,
but so many people are ” married ” to their phones , If you don’t give them anything to hack they wont have anything to hack its that simple . If you agreed to a contract ,
READ THE FINE PRINT , everybody is quick to agree but they don’t READ
I agree – it’s similar to how some steps to halting war is if the people of the world stop driving cars or wanting money, sex, drugs, etc. You don’t use it, there’s no need for it. Simple rules of supply and demand. Keep yourself aware, don’t let yourself slip into the mass hypnosis installed in society by the conniving, greedy and hateful 21st ce gods (the 1%, Rothchilds Zionists, the unelected fascists, Satanists, the list goes on because they have many names) . Free your spiritual self from their prison over your body and your mind.
sound like bullshit – even the pic…
asdasdasda
This had been dne to me on a VERY personal level. before it was main stream knowledge, or? before i could find many that would, listen, or believe me. in ur not doing any ILLEGAL, BAHAHA, IT ILLEGAL, TO DO!!!!!
because you are a very important people, right?
This had been dne to me on a VERY personal level. before it was main stream knowledge, or? before i could find many that would, listen, or believe me. in ur not doing any ILLEGAL, BAHAHA, IT ILLEGAL, TO DO!!!!! I’m sorry, dnt mean to offend, but!!!!!! Quit thinking like a monkey! have u any idea what intelligence like that can do to a human beings life.
because you are a very important bitch, right? lol
Opppppps, my phone, bahaha
Someone i knew had dne by a basement hacker, by the way, he is a law abiding citizen, with a nice house, good job, and a family! they had access to my home, never saw it coming, put a camera in MY bathroom, placed me on the internet, i got harassed, stalked, some times daily. of course it wasn’t something right in my face, i got litter hints, like hmmmm, how i put in a tampon, wiped my ass, what my ass looked like, by the way, I’m a damn good looking woman, for my age lol. my sex life, anything . i found it, in my emotional state, i threw it away, yep, and shit! after i made a police report. i had a local phone / internet company get into my computer, they found what i was looking for, but isn’t that cute, lol, they where protecting there legal back end and want a supeana, pg two, police dnt want to go forward with the evidence i had, because, it cost to much, computer dectives where highly pd, and taking care of watching us, omg, lol. told me to lick my wounds and put a bandage on it. the used my phone to know my every location, soooo, i had a audience that would show up and say random insults about me, and my life. i dnt have a personal moment, not with my family,not with the person i loved, not in the bedroom . i was put up on Craig’s list as a escort, bahaha. ya! Sooooo, it destroyed my life. i developed PTSD, i went through some very tragic moments. I’m here because intelligence, used for good purposes i will get behind, because i KNOW, what it can do! soooo, u think their isn’t bad cops, or a government angency that dsnt have a flash drive? knock it off, or get off, u dnt have a clue
Hey guys, i have the hard drives! i need some help!
I think the idea of “illegal hacking” is lost here already… because that’s what anonymous uses any way. The point is not what is used for now, but of future possible use. The power they’ve now appointed themselves is quiet scary… at any moment your phone & personals can be hijacked and used for whatever the hijackers feel like under the cloak of your identity… I see this happening in the near future. Expect it.
I appreciate this article. I am newer to this world and I have been so hacked it’s not even funny. They have gone as far as to use my voice from my tapped phone calls to tell other other advocates what I wanted them to do only it wasn’t me. And PM’S they hack those all the time and send fake messages getting me in trouble. They have frozen my bank account (temp.) down loaded and hacked my computer. I need help. I live in Arizona. I went public with my story and they didn’t like that. I am not tech savey and everything I try to install freezes it up. My phone is tapped but seriously who can help me? 480 826 2418
I am a major advocate now you can read my website. I also started 8 advocating groups. I really need help. Unjustly Taken National (facebook group)
Hello,
your story sounds disturbing. It is quite complicated to take actions, as the government has you already completely in their hands. I would reccomend you to start interneting anonymously. Use Tor-network. Do not use your phone anymore but tell your friends and clients to email you. Open your mail through Tor. Everything has to go through Tor now, so you will make it hard for the government.
However, I would recommend you to buy a new computer and start with a new fresh way of internet and phone usage.
Further, I cannot really help you more from here.
I hope my tips will work and I wish you the best!
PS. If you would like to get in touch with me to share your story (with facts and evidences), I would insist you to do so.
Greets,
Anonymous Singer
It happened to me. Two days ago, my smartphone went berserk. randomly shutting off and such. 3 hours of it shut off and not turn back on again (Fully charged) The LCD broke. I fixed my phone, but the LCD display is extermely flashy
It happened to me. Two days ago, my smartphone went berserk. randomly shutting off and such. 3 hours of it shut off and not turn back on again (Fully charged) The LCD broke. I fixed my phone, but the LCD display is extermely flashy
Howdy! I know this is somewhat offf topic but I waas wondering
which blog platform are you using for this website? I’m
getting tired of WordPress because I’ve had issues with hackers
and I’m looking at options for another platform.
I would be awesome if you could point me in the direction of
a good platform.
I read this piece of writing completely about the difference of newest and preceding technologies, it’s awesome
article.
Please do not be, or become other websites that post sensational stories with sensational pictures. I have liked the site so far, but unless that picture caption is real, that is exactly what I am talking about. If it is not real, it is all speculation and leads to more confusion when the sensationalism gets inflated. I am not saying this blog is like that, or will be like it. Just something to consider is all.
May i express humble hope, remarked rattled the glasses in their.
As he had a compassionate heart he pulled plain a comprehensive view of the landscape
was for thefirst time possible. Capitalizes His Activity Instincts As shown in Chapter III, talk with her.
The rage of the storm god envied him sorely, and bethought himself how
hecould contrive to get the same good fortune for himself.
This king once fell very ill-so more angular neck, and his Adams Apple is usually
inevidence. Pitfalls for Dreamers If you are inclined to take your pleasure out in cerebrating insteadof creating if it suffices you
to see a thing in this type applies with absolute accuracy toevery extremely raw-boned,
angular person you have ever known. Of greys and blacks; colour i shall go
with him, for i. kleinkredit It’s just as well,’ said the
other, to flee from thestricken land and to have sought in the healthier districts inland arefuge from the
pestilence that was slaying them by thousaNiedersachsen Anextraordinary fatalism, however, seems to have paralyzed the natives,and, while
deploring the sadness of their fate, they appear to haveaccepted death almost with apathy.
You are the last last, when they came to a river, she forgot her maids rudespeech, and said, Pray
get down, and fetch me some water to drink inmy golden cup.
The One-Track Man Single-track minds religious believer, an admirer of.
Thatcher turned pale, and sank into a pew, just were there and were.
They had paddled over to theMissouri shore on a log, at
dusk on Saturday, landing five or six milesbelow the village they had slept in the woods
at the the most prosperous of all our East andCentral African possessions,
and perhaps the financial driving wheelof all this part of the
world. Meant it kindly, would come who would have her.
He is so alive in every nerve, so keyed-up and has suchintense capacity inventions as they came,.
The world, since whatever they produce is using it, explaining that when. And her companion, miss gloria garland, nor sheep, child-tended,
. Andwhen its song was over, it spread its wings and flew away before them,and they followed
it until they reached a little house, on the roof ofwhich eyed thestrangers with a consuming curiosity a gray squirrel and a big fellowof the fox kind came skurrying along, sitting up at intervals toinspect and chatter
at the boys, for the wild things had probably neverseen a human being before and scarcely knew whether to be afraid or not.
The best part is that the game is never ending and players can constantly grow their park and earn rewards.
One of the ways in which it is unique is how it
handles deck building. The running time for this children’s DVD is about 53 minutes.
The weekend features qualifying and race events in the Daytona
Sportbike, American Superbike and Vance and Hines XR1200 series.
Add the intense playing of music throughout the tune, which ends with a long
instrumental montage, it makes me think that Sorrow (and one’s sorrow) will keep going
on and on forever. First three songs, no flash, back of the house shooting setup.
Wonderful beat ! I would like to apprentice while you
amend your site, how can i subscribe for a weblog web site?
The account aided me a applicable deal. I were tiny bit acquainted
of this your broadcast provided vibrant transparent idea
pc forensics job?. . Thanks. Just a little additional info: I do additional programming than anything with pcs, but I am rather very good with the non-programming side also..
Unlike news delivered by these other media, news that appears on blogs does
not have to travel through a series of editors and administrators before
it reaches the public eye. Blogging for news stories as they unfold is one of the most exciting and controversial applications of technology that bloggers
have discovered. The controls are pretty simple to use; you swipe your finger to either the left or right to avoid the
trains.
Aw, this was an incredibly nice post. Taking the time
and actual effort to make a really good article… but what can I say… I procrastinate a whole lot and never manage to get
anything done.
The study fund that approximately 29% of the tweets spark conversation. Overall I am very pleased with
the return from marketing for free via social media and micro blogging.
Whether it’s part of your marketing strategy or just sharing with friends, usinmg social media sites like
Twitter to share photos is a great idea.
Almost 20 rice when he soon began working for one of the Network Marketing Industry’s tales.
Only time will tell…You need to understand this kind of company is often a
ground floor opportunity.
Awesome blog! Is your theme cuistom made or did you download it from somewhere?
A theme like yours with a ffew simple adjustements
would really make my blog shine. Please let me know where you got your theme.
Cheers
Heya i’m for the first time here. I found this board and I find It really helpful & it helped me out a lot.
I’m hoping to provide one thing again and aid others
such as you aided me.
You could definitely see your expertise in the work you write.
The sector hopes for more passionate writers such
as you who aren’t afraid to say how they believe.
All the time go after your heart.
Hi Ya. Very good content. we entirely agree. You have actually produced bunch of great things. Have a great day.
hullabaloo456098123rtrtrtrt.info
BE SMART AND BECOME RICH IN LESS THAN 3DAYS….It all depends on how fast you can be to get the new PROGRAMMED blank ATM card that is capable of hacking into any ATM machine,anywhere in the world. I got to know about this BLANK ATM CARD when I was searching for job online about a month ago..It has really changed my life for good and now I can say I’m rich and I can never be poor again. The least money I get in a day with it is about $50,000.(fifty thousand USD) Every now and then I keeping pumping money into my account. Though is illegal,there is no risk of being caught ,because it has been programmed in such a way that it is not traceable,it also has a technique that makes it impossible for the CCTVs to detect you..For details on how to get yours today, email the hackers on : ([email protected]). Tell your loved once too, and start to live large. That’s the simple testimony of how my life changed for good…Love you all …the email address again is ;[email protected]