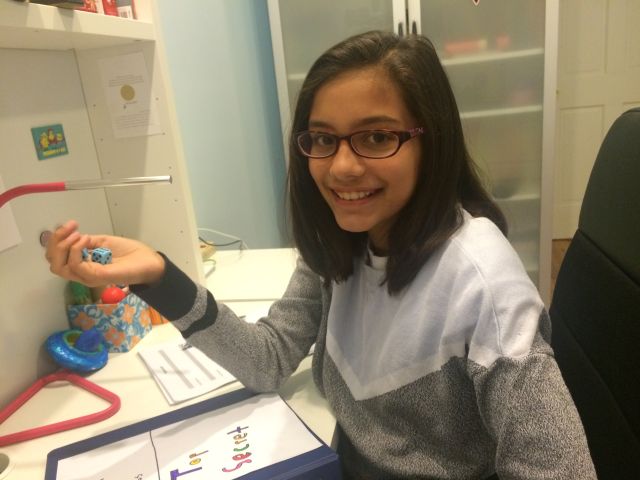
11-year-old Mira Modi, a New York City sixth grader, uses dice rolls to generate and sell cryptographically secure passwords for $2 apiece.
“This whole concept of making your own passwords and being super secure and stuff, I don’t think my friends understand that, but I think it’s cool. I think (good passwords are) important. Now we have such good computers, people can hack into anything so much more quickly,” she says.
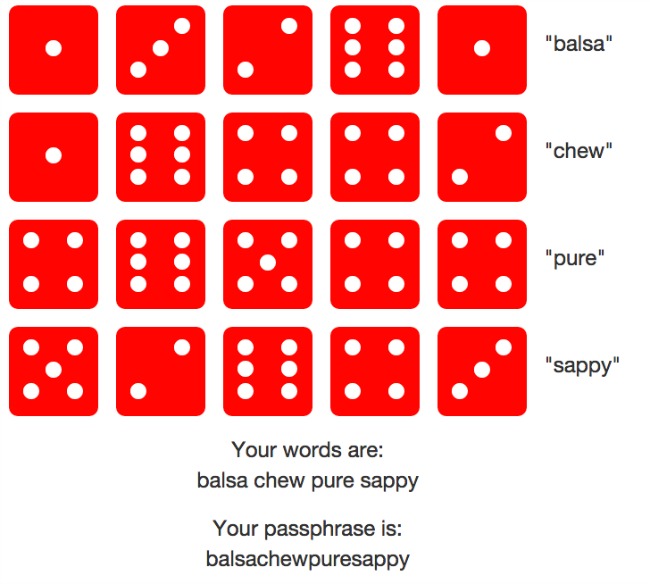
The young entrepreneur behind dicewarepasswords.com, generates the passwords using a system called Diceware to create strings of words that are easy to remember but difficult to crack. In Diceware, digits revealed by rolling of dices are matched to English alphabets listing and a random and unique password is created. Because every time a random pattern is created, every password is unique and difficult to be decoded.
Mira is making about $12 per hour, one-third more than New York State’s $8.75 minimum wage, selling strong passwords.
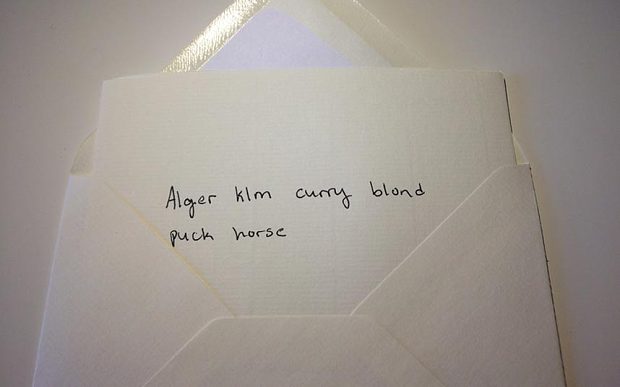
Each time an order comes in, she rolls the dice and looks up the words in a printed copy of the Diceware word list. She writes the corresponding password string onto a piece of paper and sends it by postal mail to the customer. Once her customers receive their hand-written passphrases in the post, they are advised to make minor changes like capitalizing letters or adding symbols to ensure their uniqueness.
Mira is the daughter of Julia Angwin, a veteran journalist at ProPublica and author of Dragnet Nation. As part of her research for the book, Angwin employed her daughter to generate Diceware passphrases, but Mira had other plans – to turn it into a small business. Mira writes on her website:
“I started this business because my mom was too lazy to roll dice so many times, so she paid me to make roll dice and make passwords for her. Then I realized that other people wanted them, too. I personally find that my Diceware passwords are surprisingly easy to remember. However, I only use a few Diceware passwords for important accounts. I use a password manager, 1Password, to create and store passwords for my less-important accounts.”
Arnold Reinold, creator of Diceware, tells Ars Technica:
“I am tickled to hear this, and no, I haven’t heard of anything like it before. Obviously from a security perspective it is much better to generate your own Diceware passphrase in private, but it is unlikely she is working for the bad guys, and any effort to publicize the importance of strong passwords is for the good. I just hope she isn’t sending the generated passphrases to her customers by e-mail or storing them on her computer. I wish her well.”
But Mira understands the concerns and therefore got those covered.
“People are worried that I will take your passwords, but in reality I won’t be able to remember them. And, I don’t store them on any computer anywhere. As far as I know there is only one copy of your password. The passwords are sent by US Postal Mail which cannot be opened by the government without a search warrant.”
This Article (Meet The Girl Who Creates Unhackable Passwords Using Dice Rolls AND Makes $12 Per Hour!) is free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ.com.





This is common sense and not really special as it looks. unhackable passwords are so easy to create, i wish i got paid for that.
Those look normal password… Passwords that everyone use and there ain’t such thing as unhackable password.
Isn’t the average value of many throws 3.5 on a 6 sided dice? Some of the words may be more likely to get chosen each time.
Ridiculous people would actually pay for this. There’s many programs that will not only keep track of your passwords but will randomly generate them for you for -free-. Dashlane is one of them.
Because no one ever hacked a website full of passwords before. Moron.
Not unhackable at all.
The longer the password, the harder to crack. There’s no such thing as an unhackable password. Its just takes the password cracker longer to find the right letters and/or numbers. Its called a brute force attack. Its pretty much goes through all possible alphabetical and numerical combinations until it finds a match. That’s why 1 letter or number could add an extra couple hours to the cracking process unless you have a good computer, then it will only add a half hour or so maybe less.
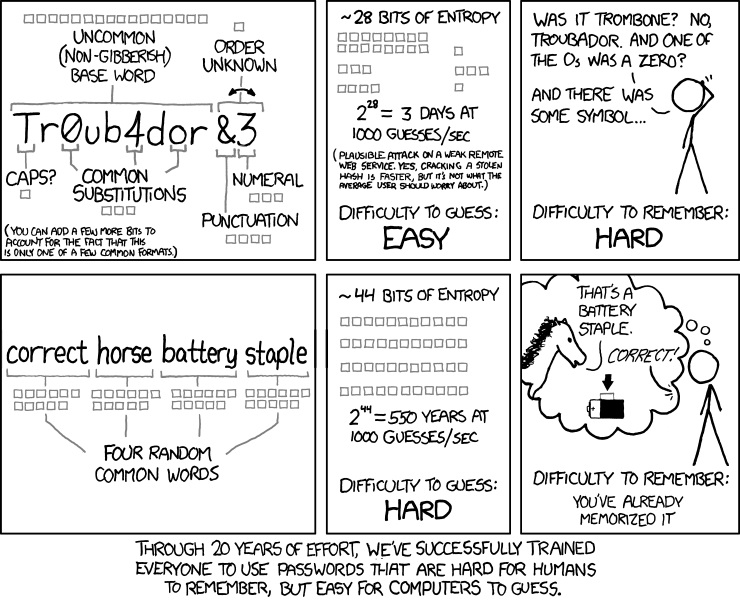
I would like to reply to Hunter; Modern brute force attacks don’t rely at all on the length of your password. This is because passwords longer than 8 characters consisting of truly random characters (even restricted between 0-9 and a-Z) are considered to be pretty much unfeasible to crack. However, these types of passwords are hard to remember by humans and we therefore use words in our language to help us remember better. That’s where dictionary attacks come in. Instead of combining random numbers and letters to make up a brute force attack, entire words are combined with both numbers and letters in order to execute the attack. Which means if your password consists of two or less words, even with the first letter capitalized and a number at the end, then your password is weak regardless of length.
Ah, I see.
Dear Mira,
Why don’t you put your list of nouns, verbs and adjectivs in an excel sheet, index them, take the good old vlookup fromula coupled with a random number generator and patch them together. You only need to hit F9.
And some people are paying for this ????????
It’s like $2 a password, really not a big deal. Some people are so computer-illiterate that they’d appreciate any help in this vein. (Sad part is, of course, that the really computer-illiterate won’t even know about this girl.)
God, smell the testosterone in here. Ignore the clickbait headline, I doubt there are any truly unhackable passwords in the world, what this girl is doing is still pretty awesome. If someone wanted real security all they’d have to do is send her snail mail with a money order and a false name on it from a P.O. box. I don’t see any password generator website offering a service like that. But do go on with your little circle jerk talking trash about her, you’re just jealous you didn’t think of it first.
Passphrases, not passwords.
Those passwords are not unhackable. For a real unhackable password put random numbers, letters, symbols, unicode (if able), etc.
EX: M$vT8p%2Qz^B@4
An extra character is so much more effective than using symbols etc.
Let’s take an 8 character password. You decide to use random symbols as well as numbers and letters. Using the regular set of allowed characters that would be an extra 29^8 layers of security. That is assuming that the brute force cracker being used didn’t already look for symbols, which would be incredibly naive, so in reality it isn’t any more secure at all against such a method. Sure, it’s harder for a human to guess. Your dog’s name “fidothedog” = easy to guess, “f!D0+hEDo&” = hard. A program doesn’t care though, they’re both the same to a computer.
In a standard password there are 65 allowed characters. In an 8 character password there are 65^8 (or 318644812890625) possibilities. Add in an extra character and that takes it to 65^9 (20711912837890625). The smart folk out there will realize that this will take 65 times longer to crack.
I know what I’d rather use.
General rule of thumb – 9 or more characters, random characters (NOT words, that would leave you vulnerable to a dictionary attack), not your mother’s birthday etc and you’ll be fine.