
Since we are talking about passwords, let us get right to the point: security specialists suggest using tough-to-hack passwords or passphrases with a mixture of upper case and lower case letters, numbers and symbols. The primary reason people do not create such passwords or phrases, is that they are not easy to memorize. In addition, most applications or online services do not prompt users to use a strong password.
In fact, a study that examined 12,000 online services (cloud, email, etc.) discovered that only 6.5% wanted users to have strong account details. The study also found that only a few of the online services required average passwords – that is only requiring numbers and letters— and a frustrating 79.9% of online services permit users to keep weak passwords – meaning passwords that have lower or upper case letters.
In many cases, the researchers also found that a lot of people also use the same passwords on many different websites. However, if even one of your passwords are compromised, it could potentially have a ripple effect of your other online passwords. According to Joseph Bonneau, a Postdoctoral Researcher at the Department of Applied Crypto Group at Stanford University, the average person has their accounts on a minimum of 28 different online services. These outcomes were attained by examining business that utilize cloud services. In total, over 17.5 million users were examined, and Joseph Bonneau discovered that more than 33% of the users uploaded information that could easily identify as cell phone numbers, home & business addresses, bank account details, social security numbers, etc.
Remembering long and complex passwords can be tricky; as a result, more and more people are beginning to use software that helps its users organize their passwords and password vaults like Dash Lane, Sticky Password or Last Pass (click here to check the complete list of password vaults) in order to keep their email, social media, device and other passwords safe and secure.
Recently, many of these password vaults have been a focus for online criminals. For example, attackers hacked LastPass master passwords, the same passwords that are used to keep all the other passwords safe. However, as the company had encrypted the stored passwords, the hackers were unable to gain access to the main passwords that the users stored in their accounts.
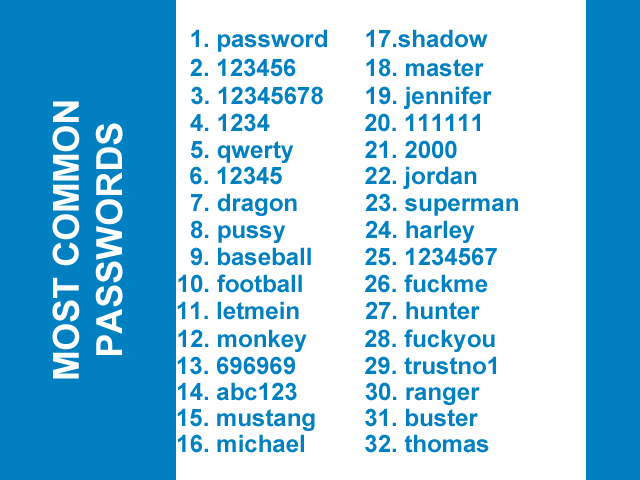
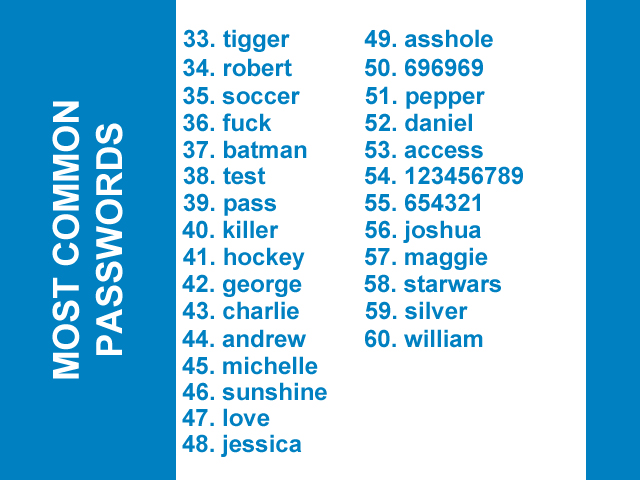
However, hackers do not really need to thieve a password to damage your account; if we keep creating passwords that are in the top 100 list, then they will eventually guess vulnerable passwords. Security firms have analyzed over 10 million passwords from various online storage services that sadly are on the deep web market, and found that more than 9% of people use the top 20 passwords on the list. Which indicates that with under 20 attempts, any individual would be able to login to all ten accounts.
Whereas these passwords are simple and easy to remember, people are beating the very system that is supposed to guard their details. The most highly used password is “123456,” and it is so frequently used that it jeopardizes 4% of all passwords — users often adds these numbers after their name or after an easy word that they can remember. Using passwords like the ones on the list, is like putting your house key under the doormat in a not so safe neighborhood.
HOW TO PROTECT YOUR PASSWORD
If complicated distinctive or passwords that are difficult to memorize are required for every sing account, and software like Last Pass that assist their customers to remember such passwords or passphrases are threatened, then this brings a question to mind; can my password really protect me? Increasingly, it is coming to be true that other verifications and protection systems are required to shield fragile data. Also, companies like Dash Lane, Last Pass and much more have added an extra set of security feature called the multi-factor verification system to secure the login systems after the breach of Last Pass master passwords. For those of our readers who do not know what a multi-factor authentication system is; once the user adds in their details, such as their username and password, the company that is using the multi-factor system sends a code on the registered phone number. Then the user is required to add that code on the page to proceed further. This extra part makes it very difficult for a hacker to gain access to an account even if they have your password, because every time if they use your password you will get a text message with a code and then you would know that someone is trying to access your account to which you can even change your password. However, less than 16% of the online storage services use the multi-factor verification system. And for those that do, i.e. Google Drive (that is if you have activated it on your primary email), then it only asks you once (also, if you click on the box saying remember me on this PC) which can be dangerous. Web sites that store users data should design an algorithm to pattern users everyday behavior (like Freelancer – it informs you if you are signing in from an unknown location) and discover abnormal access attacks, and bars the login or demands multi-factor verification login on the basis of the fishy activity. Such type softwares are used by banks as well, if they detect a credit card being used in a different country or if the software detects an odd card transaction then it automatically declines the transactions, which in result requires you to call the bank and present further information showing your identification prior to approving the transaction. So in order for you to stay safe and protect your valuable information we reckon you to create strong passwords as well as use two-factor authentication system (if available) and additionally use password vaults to enhance your protection and password management.
FOR A COMPLETE LIST OF MOST COMMON PASSWORDS, PLEASE CLICK HERE
Source: Password Random, IFL Science
You want to support Anonymous Independent & Investigative News? Please, follow us on Twitter: Follow @AnonymousNewsHQ
This Article (Is Your Password In Our List Of Weak Passwords) is free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ.com.





13 and 50 are the same. I call bullshit.
There is a space in the second one. PWN3D!!!1!oenoneone!
If you have trouble coming up with a strong password that you can remember, one way I learned to do it is to use song lyrics. Pick a line from one of your favourite songs then use the first letter of each word for your password. Easy to remember if you remember the song and really hard to guess.
I have used Dash Lane for almost 2 years and have been very happy with it. I am also proud to say that not a single one of my passwords is on that list–of course, I have a background in Network Security, so I have always had the mindset of keeping my electronics/Internet devices safe.
If you really can’t remember your username/passwords…write them down with the site’s name on an index card and then store is somewhere private AWAY from the computer desk. Like in another room! At least then only family members are able to get your passwords…HAHAHA
Is it so hard to integrate just some special characters in your password?
Just make from thomas -> !thomas#123; now duplicate it: 1thomas#123!thomas#123
This is, where a secure password starts. Is this difficult?
https://xkcd.com/936/
nuff said
correct horse battery staple (technique) – it is easier to remember 3-4 words than 8 or more random characters and it would take brute-force trillions of years to crack such a password
I think what can sometimes make it difficult for some, is when one is required to change passwords frequently enough (another matter of security, as given enough time something can be brute forced), that some have trouble coming up with a new secure password they will then remember. This can lead to other issues.
When I was taking a class in Novell Netware administration in college, in I believe it was 1998, the teacher went to demonstrate this fact. He had us set the password policy to require one to change their password daily (which would be a little extreme). What was shown was:
– 80% of the class forgot their passwords. He was like “ok, you’re the administrator, you fix it”. Of course the administrator was the one who forgot his/her own password in this.
– Some in fact did respond to the utterly stupid, cycling through dog1, dog2, dog3, etc
– Yet other students approached this by writting their passwords down and putting them on stick em notices they’d place under the keyboard.
After this fiasco, and him leaving the class to discover this for themselves, then then explained both the nature of computer security, the balancing act one must achieve between securing it, and also having things accessible for authorized users, the implications an admin could face based on their choices, both in terms of securing it and in terms of having to handle forgot passwords and issue resets routinely, and how some users would approach the issue and the implications of that as well (such as those who wrote their’s down). Naturally one wants to harden things enough that the guy down the street is the softer target, and relative to what a hacker (or perhaps more accurately in some cases cracker) could get from the time/effort they’d expend in trying to crack into one’s own system, what they could get out of it just wouldn’t be worth the time/effort, given there are softer targets they can accomplish their goals with instead. Naturally if someone has stuff on their system that is more valuable then the guy down the street however, they will need extra security as it’s now worth it for someone to spend more time with their system/network.
What I find totally ridiculous however, is that Blizzard for instance with their battle.net passwords, makes everything lower case in their system, even if you type both upper and lower case letters. Their argument is it’s easier for people to remember, but it does make things less secure. At least they have added an authenticator code one must enter in addition to the password, as an additional step, if one sets it up however.
Thanks for the tips and insight, glad to say haven’t used any on the lists