The Tor network developers have been secretly working on their next iteration of the new Tor Network. The Onion routing protocol is used to generate a new, stronger, and much harder to crack anonymous communications system for hackers.
In order to further advance the Tor Project, the developers team schedules are brainstorming and planning their meetings at a regular intervals, with the most recent meeting taking place just last week in Montreal, Canada.
In this meeting, the team had tested their prototype of the next generation of their Tor Network, which they are working on, on top of a newly revamped Onion Protocol. The future for Tor Communications will be more secured than ever before.
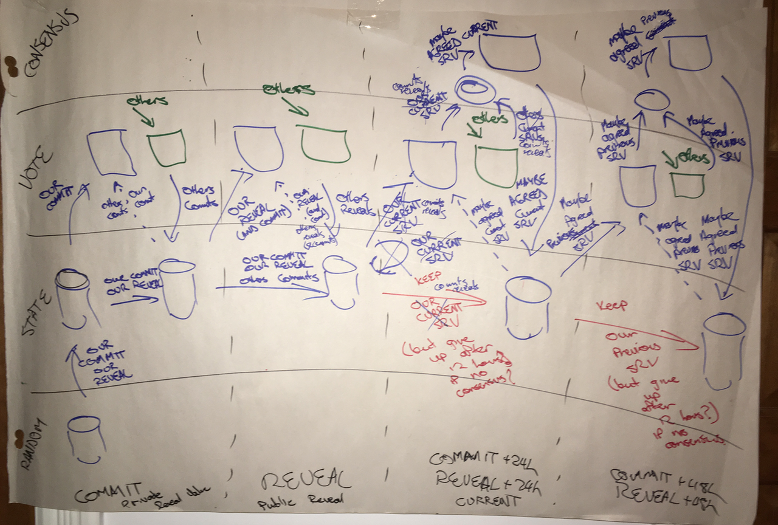
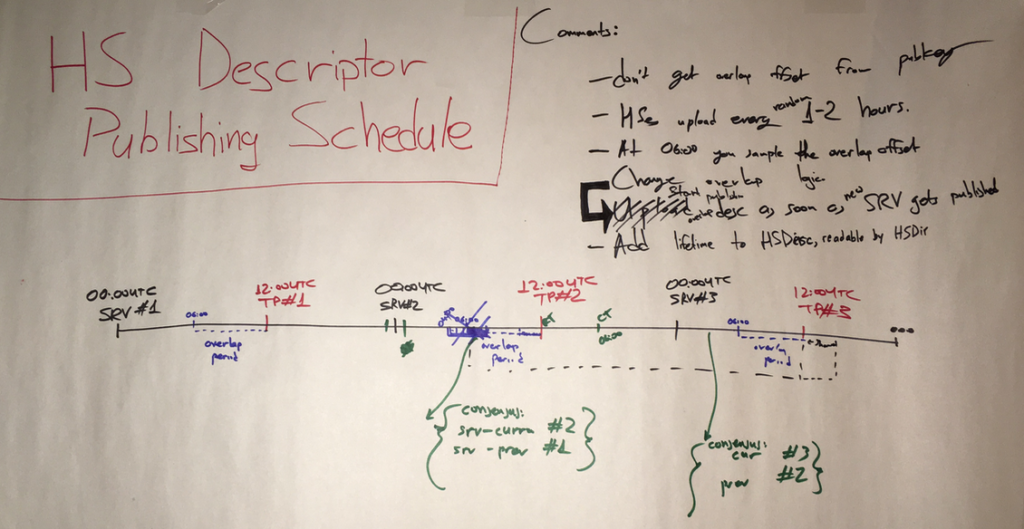
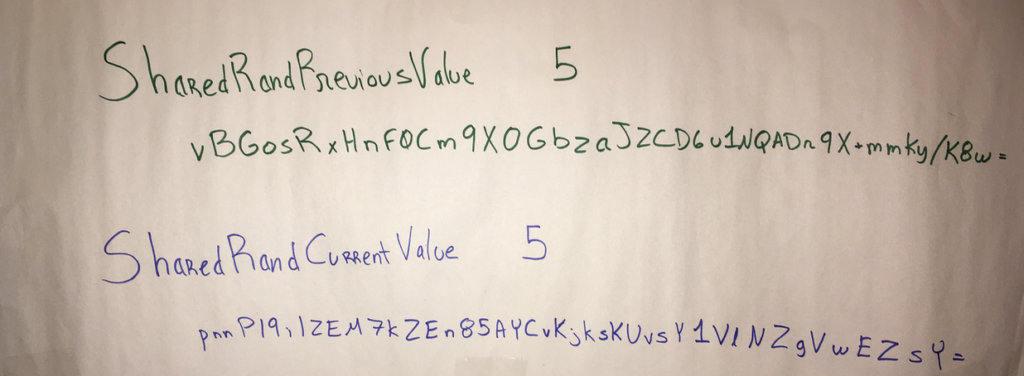
The Tor Team states that they will implement a new line of mechanisms to generate random numbers, in which has never been seen before on the Internet.
In secure communications, as well as encryption settings, the new random numbers are a valuable and critical importance to this project, as it will then serve as the base for generating new encryption keys; as we all know, the stronger the algorithm based on the random numbergenerated, then the harder it will be for a threat group to be able to crack, let alone guess, the number based on known patterns.
TheTor Project is stating that their new distributed RNG system is so strong, that not even those who had designed the new Tor protocol will be able to predict the output of the system.
At this point in time, the distributed RNG system is in the code review stage and then onto the auditing stage.
“It’s a complex system with multiple protocol phases that involves many computers working together in perfect synergy,” said the Tor Team Montreal Web Page, “As far as we know, a distributed random generation system like this has never been deployed before on the internet.”
Sources: TorProject.
This article (Tor reveiling a never before seen ditributed RNG in order to generate truly random numbers)is a free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ





Tor = DARPA honeypot.
Abstract random mirror arrays generating and random time seeded titling nodes. Any greycracker would admit nearly impossible to piggyback such a amount of data blocks in thar protocols that reset over and over by such similar methods. Darpa? The NSA would need a supercomputer 8x more productive than what is now.
Near true random time based seeding with near true random list near true random mirroring is not a condition of running a simulation to find appropriate paths, but multiple simulations on the equations that are time seeded themselves; and depending how they stretch out the algorithms for each procedure is even more daunting, petabillions in thousands of years for current supercomputer runs.