
Our smartphones are always within reach and their location is generally the same as our location. In effect, tracking the location of a smartphone is practically the same as tracking the location of its owner. Since users generally prefer that their location not be tracked by arbitrary 3rd parties, all mobile platforms consider the device’s location as sensitive information and go to considerable lengths to protect it: applications need explicit user permission to access the phone’s GPS and even reading coarse location data based on cellular and WiFi connectivity requires explicit user permission. In this study we show that applications that want access to location data can bypass all these restrictions and covertly learn the phone’s location – these are the technical, and scary, words coming from Stanford’s research paper.
So what does that mean? According to the latest research in the field of mobile operating systems, it was discovered that it is possible to track cell phones via accessing power usage log(s) or files of a device. This particular data set does not require user permission to be shared; it is already set to that status by default.
The credit for this goes to researchers at Stanford University along with help from the Israeli defense company, Rafael. This technique that they have created, dubbed ‘PowerSpy’, is able to collect information regarding the Android phone’s location. It simply does that by tracking how much power was used at a certain time.
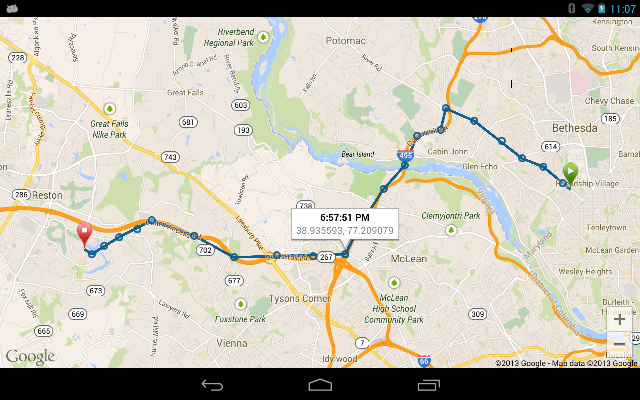
Image Source: Google Image – An image of self-tracking enabled via Google Maps on an Android operating system.
How much power is used depends on a variety of factors. For instance, the closer in proximity that the phone is to the transmitter, the less power is required to obtain signals but the further it goes from the tower, the more power it will require in order to keep itself connected. Objects such as buildings, trees and other things also have an impact on the amount of power needed from the battery, as these obstacles block the phones signals thus they are power drainers.
“A sufficiently long power measurement (several minutes) enables the learning algorithm to ‘see’ through the noise. We show that measuring the phone’s aggregate power consumption over time completely reveals the phone’s location and movement,” the researchers explained.
Researchers conducted a test in which they collected data from mobile devices while driving around the Bay Area in California and also in the Israeli city of Haifa. The product that was tested was an LG Nexus 4. By using the technique they created, they were able to identify and locate the target path with an accuracy of ninety percent.
Don't want to be tracked. Just turn off your phone : Spies Can Track You Just by Watching Your Phone's Power Usage.
— Anon.Dos (@anondos_) February 23, 2015
But with this entire hack, there is a loophole. Experts say that is impossible to gain data if the hacker has not used the same route before.
“If you take the same ride a couple of times, you’ll see a very clear signal profile and power profile. We show that those similarities are enough to recognize among several possible routes that you’re taking this route or that one, that you drove from Uptown to Downtown, for instance, and not from Uptown to Queens,” states Yan Michalevsky, one of the researchers from Stanford.
He further stated that if a person installs an application such as Angry Birds, that requires internet but does not ask for any location permission, it will still gather information and send it back to the hacker to track the target in real time, as in what routes one has taken and where did that person drive/travel too.
Is It Possible to Track Smartphone Location By Monitoring Battery Usage? Checkout PowerSpy — http://t.co/oXydHDWoPY pic.twitter.com/JJitYGVpaD
— The Hacker News (@TheHackersNews) February 22, 2015
One said that if a phone has only a few applications running then it would be easy to track the device as the power being used by the device is more consistent, versus phones with more apps as those apps use processor and RAM randomly, ending up with a data of unpredictable power usage.
This is not the first time that Michalevsky and his gang have used weird phone parts to disclose user sensitive details. In 2014, with the help of expert cryptographer Dan Boneh, they were able to discover a means in which they were able to exploit the gyroscope sensors in a phone and fashion them into crude microphones. They did that by picking up digits spoken in to the phone, and with this they were even able to distinguish between male and female voices by the vibrations. “Whenever you grant anyone access to sensors on a device you are going to have unintended consequences,” says Professor Boneh at Stanford University.
PowerSpy – How to spy on mobile users by monitoring the power supplyhttps://t.co/iPvVirsCh7#securityaffairs #PowerSpy #mobile #spy
— Security Affairs (@securityaffairs) February 23, 2015
However, Michalevsky says that PowerSpy is another reminder of the danger given to us by the un-trusted applications as we allow them to access a sensor that picks up more information than it was originally allowed to. He ended it by saying, “We can abuse attack surfaces in unexpected ways to leak information in ways that it is not supposed to leak.”
There is nothing that can be done to stop this as certain applications such as Facebook, Twitter, Instagram and a like application ask the user to provide them their current geo-location. And also the data from the phones power supply is freely available this is something that Google seriously needs to look into.
Anonymous recommends: Protect your PC & mobile devices from hackers & governments & surf anonymously
SOURCES:





And that is where the google’s so called “games”comes in – take Ingress for instance. All users playing this game are basically collecting data needef for this exact metod of tracking and they are doing it willingly for free all around the world.
What about this new thing that is going on with the phone batteries? supposibly the Gov is planting a bug hat is attached to the bat and it feeds on the bat power to oparate. Its all over faebook and you see them all taking this “bug” out https://www.facebook.com/richie.mari/videos/10152801055996082/ how much thruth is to that?