We know from the Snowden archive that western intelligence agencies are attempting to manipulate and control online discourse with intense tactics of deception and reputational destruction.
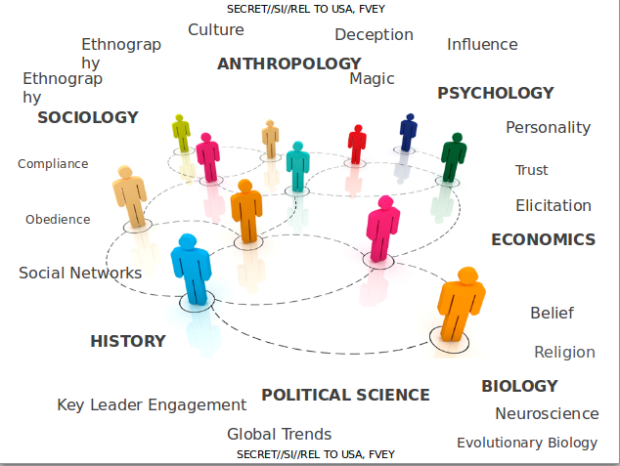
The Intercept has intercepted some secret documents that point to what Snowden revealed. The documents lay out theories of how humans interact with one another, particularly online, and then attempt to identify ways to influence the outcomes or what is termed as “game” it.
The documents entitled ‘The Art of Deception’ were strangely obtained from the Joint Threat Research Intelligence Group (JTRIG) by The Intercept. It were based on four classified documents presented to the US’s National Security Agency and the other four partners in the so called English-speaking “Five Eyes” alliance made up of Australia, Canada, New Zealand, the United Kingdom and the United States.
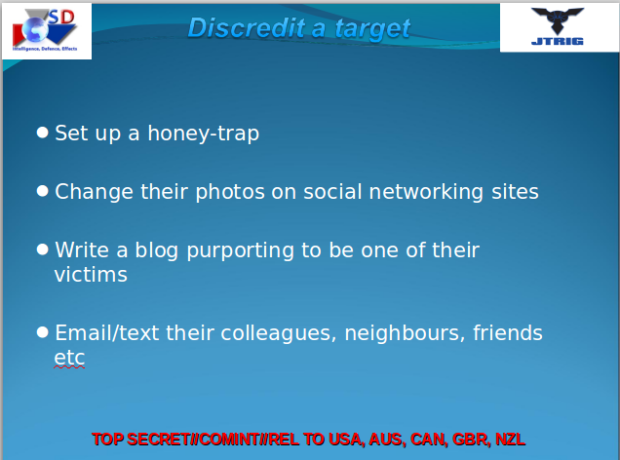
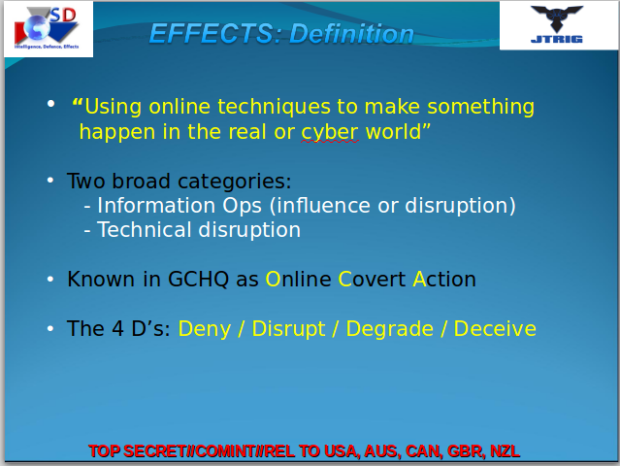
The documents is purely training for online covert operations spearheaded by the British’s Government Communications Headquarters (GCHQ) that include the monitoring of YouTube and Blogger, the targeting of Anonymous with the very same DDoS attacks they accused “hacktivists” of using, the use of “honey traps” (luring people into compromising situations using sex) and the creation of destructive viruses.
These revelations found in the documents shows clearly that Western Intelligence Agencies are attempting to control, infiltrate, manipulate, and warp online discourse, and in doing so, are compromising the integrity of the internet itself.
Internet experts who understand the documents better due to its technical terms say the JTRIG is using two strategies to carry out the operation.
The first one is to inject all sorts of false material onto the internet in order to destroy the reputation of its targets and secondly, to use social sciences and other techniques to manipulate online discourse and activism to generate outcomes it considers desirable.
To see how extremist these programs are, just consider the tactics they boast of using to achieve those ends: “false flag operations” (posting material to the internet and falsely attributing it to someone else), fake victim blog posts (pretending to be a victim of the individual whose reputation they want to destroy), and posting “negative information” on various forums.
The big question is how dangerous it is to have secret government agencies targeting any individuals or companies they want that have never been charged with any crime or come under any suspicion or whatsoever?
The truth here is that, far beyond hacktivists, these surveillance agencies have vested themselves with the absolute power to deliberately destroy people’s reputations and disrupt their online activities for their own parochial gains. The people being monitored have no connection to terrorism. They are not threat to national security. Why then this gross abuse against them?
For the US government, plans to monitor and influence internet communications, and covertly infiltrate online communities in order to propagate dissension and disseminate false information, have long been the source of speculation. 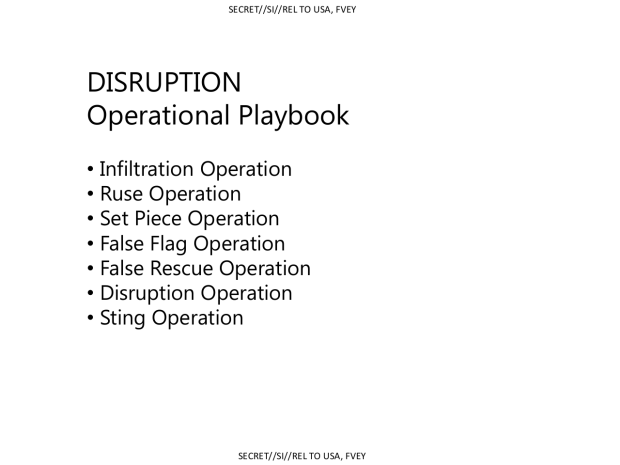
Harvard Law-Professor Cass Sunstein who is close associate of the current administration in the White House wrote a controversial paper in 2008 proposing that the US government employed teams of covert agents and pseudo-”independent” advocates to “cognitively infiltrate” online groups and websites, as well as other activist groups.
When Professor Sunstein said this, we thought it was a mere allegation. But before our very eyes, we now see the bare facts starring at us. We do not deserve this from our governments. We are not terrorists or neither are we in any threat to national security. We are ordinary citizens. The gross abuse of the internet and total disregard for privacy by western governments must end now.
Anonymous recommends: Protect your PC & mobile devices from hackers & governments & surf anonymously
Source: earthfirstjournal.org





i knew they were observing us. it was no survailance. they are going to do mass damage.