
More Edward Snowden documents have been released through Germany’s Der Spiegel, which are available for download. The documents show that the National Security Agency (NSA) and its allies have been preparing for ‘internet wars’, and that the NSA and the UK’s Government Communications Headquarters (GCHQ) feel they are so far ahead in the game, they’re laughing about it.
The documents show that the NSA surveillance programs were only the beginning of their efforts to create sophisticated digital weapons for their internet war efforts. One of the goals included is to be able to infiltrate and disable computer networks, thereby giving them the ability to disrupt utilities and other infrastructure.
The US is already capable of launching complex digital attacks that can cause physical harm, such as a computer virus known as Struxnet that was deployed in a joint operation between the US and Israel. It destroyed Iran’s Natanz nuclear facility, as well as many of the country’s nuclear centrifuges. However, now the NSA has begun to boast of having newer and more powerful digital weapons.
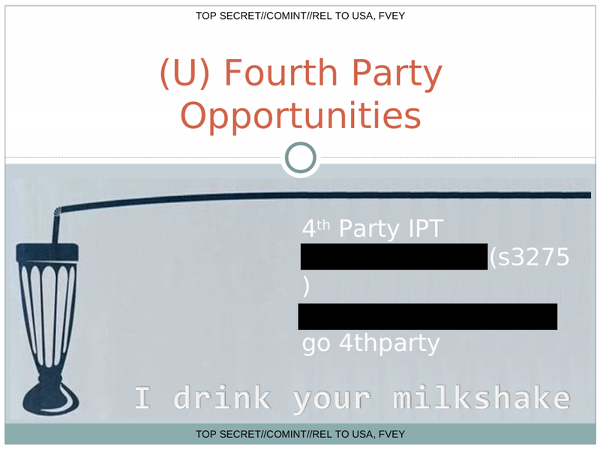
A major theme of the new documents involves ‘Five Eyes’ intelligence, or the ability to exploit the methods of its adversaries. Basically spies spying on spies. The NSA calls this capability ‘fourth party collection’.
Apparently fourth party collection is so successful, the NSA and GCHQ have been making jokes about it. In one presentation, they quoted a famous line from the 2007 movie, There Will Be Blood… “I drink your milkshake.”
It’s reported that in another presentation, the GCHQ details how it exploits ‘leaky mobile apps’ with a tool called ‘BADASS’. Spy agencies can, “glean personal information from metadata sent between users’ devices and mobile ad networks and analytics firms—data that’s not supposed to contain personally identifiable information.” Several of the slides are titled, “Abusing BADASS for Fun and Profit,” and another slide boasts, “We know how bad you are at Angry Birds.”
“It’s absurd: as they are busy spying, the spies are spied on by other spies,” Der Spiegel writes. “In response, they routinely seek to cover their tracks or to lay fake ones instead. In technical terms, the ROC lays false tracks as follows: After third-party computers are infiltrated, the process of exfiltration can begin—the act of exporting the data that has been gleaned. But the loot isn’t delivered directly to ROC’s IP address. Rather, it is routed to a so-called Scapegoat Target. That means that stolen information could end up on someone else’s servers, making it look as though they were the perpetrators.”
SOURCES:
Doctorow, Cory. Boing Boing. Jan 18, 2015. (http://boingboing.net/2015/01/18/ecstatic-nsa-spooks-delight-in.html)
Sottek, T.C. The Verge. Jan 17, 2015. (http://www.theverge.com/2015/1/17/7629721/nsa-is-pwning-everyone-and-having-a-chuckle-about-it)
WorkerAnt#11. Investment Watch. Jan 18, 2015. (http://investmentwatchblog.com/new-snowden-documents-show-that-the-nsa-and-its-allies-are-laughing-at-the-rest-of-the-world/)





Well, I’m glad I’m on the right team. We got the tools to torment, control and manipulate popular opinion around the world. World domination is near.
Seriously, they can snatch a message/file in transit by realtime scanning data packets/TCP/IP wrappers and inject it/alter ithe content so it says something they want. The sender has no idea either. Sneaky. Apparently voice talks too.
Strangely, they can’t decrypt strong encryption like freeware GPG/PGP apps. Haha. A. Simple and ancient method of secrecy using cryptic messaging.
A simple defence for everyone they renders their million dollar systems useless. Duh.
Good luck getting everyone to stop using it now.
Cypher Punks rule.
Don’t forget to tell them that their TIME is UP! VHF. We are coming to them!!! vhf.
Well, then i say: attack that system till it’s totally useless. You hacktivists have the tools.
The font and background combo make this a tough read.
Bout time to get rid of this rubbish, if you ever start telling truths on here I may come back. Article after exaggerated article nothing but bullshit
All that power and the cant get someone to repatch that phone.
Gonna be funny when the world wakes up and realize that it is the american goverment who the world biggest terrorists
Yes- AND IT,S -ABOUT – TIME TO -START KICKING – MR , PHELPS – ASS ! – : )