
Freedom of speech, along with many other things is protected under the First Amendment of the United States. The three founding fathers wrote it under the pseudonym of Publius. However, in today’s world, it is extremely difficult for people to remain anonymous over the internet – where anything you do, and every website you visit can be tracked. Our intelligence agencies have claimed that they can monitor anyone if they fall under a certain profile, and with many of the agencies abusing their power, no one is safe.
Therefore, in such an environment one asks the question of how we can post our thoughts on Twitter and remain anonymous, knowing that the social media giant can give the government our data upon their request.
Here are some techniques to help…
Understanding the Picture

To be honest, it isn’t possible to be completely secure at all times, so we need to set our goals on what we want to protect the most. Obviously, it’s our need to protect our real identity.
Using the TOR Network & Masking Your IP with It

An Internet Protocol address is a string of numbers used to identify a single computer or several computers on a given network over the internet. Unless you protect yourself, everything you visit on the ‘normal’ internet checks for you IP.
If you are using Twitter on your PC from your home, or are connected to your office Wi-Fi via your cell phone, Twitter will be able to monitor your IP. Needless to say, if you are posting your free thoughts that go against government policy, Twitter can hand your IP to any agency.
The Onion Router, to put it simply, is a decentralised network of servers. It allows people to avoid the internet’s censorship and move away from online monitoring as well as accessing the internet in disguise. Therefore, if you access Twitter via the TOR network then Twitter won’t be able to identify your real IP – one of the benefits you have using a TOR network over a simple VPN.
The TOR browser is a Firefox browser, tweaked to access the dark web, hiding your real IP address. Although using the TOR browser is the easiest way to explore the deep web and remain anonymous, it isn’t 100 percent safe. Hackers can still find vulnerabilities in the TOR browser to unmask your real IP address. Therefore, it’s important to update your TOR browser the moment it asks you.
In addition, if you really want to feel safe, then you can protect yourself by using the Tails or Qubes operating system. If you take security seriously, then this is the way to go.
Getting a Safe & Secure Email

The convenient email services of Yahoo, Hotmail, Gmail, among others, allows a free account to be made. But because it’s free, you get what you pay for – so to speak. There is no anonymity and many of these free services require you to prove your identity with a phone number.
However, you can hide it all with a provider called Sigaint – it’s a deep web service that can only be accessed via the TOR network; its servers can be online and offline.
You can also use ProtonMail – an encrypted email company that keeps its servers in Switzerland. It requires minimum signup details and works over the TOR servers. It can be accessed via the surface web and the deep web. However, to keep away from abuse, they ask TOR users to provide a phone number, for an authentication message. You can follow the instructions here to create a ProtonMail TOR-based account.
More deep web email address providers can be found here.
Getting a Fake Phone Number

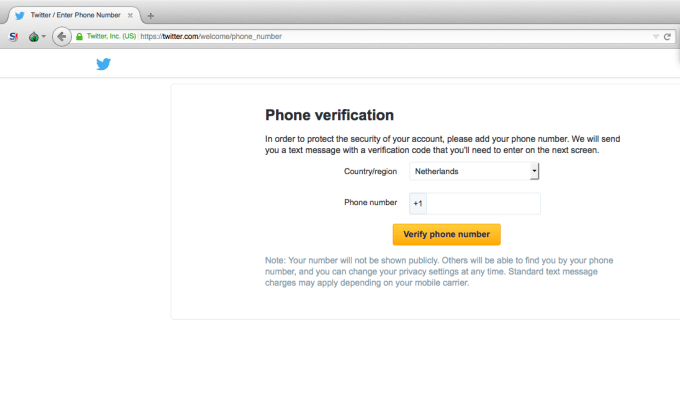
As we all know, in many countries, Twitter ‘wants’ you to give them your phone number. However, there are countries where Twitter skips the phone verification and creates the account without one.
If you want a fake phone number, there are several ways to achieve this. You can buy yourself a burner phone anonymously from any shop that won’t ask for your identification – simply use the number to create your Twitter account and then throw it away.
Be mindful however, when you purchase a burner phone, use cash and get a top-up or prepaid services, rather than using a credit or debit card. Once you buy one, the shopkeeper should activate your services there and then in the store. A better option again is to buy a SIM card from a different city or faraway place.
Since many of us are living in CCTV states, with our faces already captured on camera, the best practice would be to wait for a month before rebelling against the dark side – as most footage is erased between one day and 2 months. Do some research; find where you can buy a burner phone and use DuckDuckGo search engine on the TOR browser.
And remember: never activate your burner phone from your home, office or at your friend’s place. Use public places such as a cafe, a library – where there are no cameras or people – and for the rest of the time, keep your phone turned off.
Once you get your burner phone you’ll also need to activate it. Most companies will have a number mentioned on the back of the SIM card and better still, activate their service via their website using the TOR Browser.
Once activated you can learn your phone number by generally going into the Settings > Phone Information.
Let Us Create the Rebellious Twitter Account
Now that we have our private number and the encrypted email, it will help us to create our Twitter account. But before doing this, move your equipment to a public location. The phone will record the location in its history, so you might want to do this step as far away as you can from your residential or work location.
Now, fire up your TOR browser and open Twitter’s website and fill in the information. When it asks for your name, add ‘anonymous’, and when it asks for your email address, enter the one you created on ProtonMail. Once signed up, it’ll ask for your phone number. Once you enter the number, Twitter will ask to call or text you, so choose whatever you’re comfortable with. Once the Twitter verification is complete, get rid of the burner phone.
Also, check your encrypted email address to see if you received an email from Twitter. If you did, the sign-up process was successful. Afterwards, simply login to your new secret Twitter account, enter your new username and start tweeting.
Working on the Twitter Account
Now that your account is complete, it’s time to maintain its secrecy and remain anonymous. You must be very sure of what you are tweeting and how you tweet it – one little mistake could kill the whole operation.
A few pointers to keep in mind are, if you’re not sure about the other person, don’t interact with them. Provide minimal information on a need-to-know basis and lower your risk of leaking your identity by giving out too much information.
If you have special information, be careful about how you tweet. If you’re a member of a group that holds some kind of intelligence or information, don’t leak it yourself. Instead, contact us, WikiLeaks, or The Intercept. Once they publish the information, then retweet it. Play it safe.
If your profile gets a lot of followers, an influx of messages may occur. Again, respond in a minimal fashion. Many such strangers will do anything to extract information from you, and possibly your identity.
Most importantly, be extremely careful of the links you click on that people send you – there is a big possibility these links are malicious, and the person on the other side wants your real IP or to find a vulnerability in your TOR browser. We advise that you ignore these links for your own cyber and personal safety.
Also, make the habit of checking your TOR browser for its latest updates for the latest patches, and set your security slider to full, on ‘High’. Most importantly, use a different writing style from your original one. Professionals can analyze your writing style and compare you to other profiles for a match. Your ‘voice’ is as individual as your fingerprint.
Divide and Discreet
If you’re at work and have a thought for the day to tweet, write it down. Don’t ever use your office computer, as many organisations monitor their employees.
If you have your personal computer at your disposal, then use this instead. Also, don’t use your office internet because many companies also log the network traffic on their servers. Even though the TOR masks what you are doing, the company’s network can still log the TOR connection on the server.
Also, never follow your personal account or your friend’s account when using your anonymous Twitter account. Never login from your phone, even if the phone has Orbot or the TOR network on it. Don’t retweet your tweet from your personal account either, because you don’t want to reveal your real social group.
Never upload images to your anonymous Twitter account as it contains metadata that can be used to track you. On the other hand, uploading screenshots is a safer bet.
It would be best also, to have a group of people maintaining the anonymous account. So if giving the information to someone, ensure this is a person you can fully trust. Make rules for using the account, too. Use private and encrypted chatting software, such as Threema or Signal, to stay in touch with your team, and if you’re using Signal, then you can set the messages to disappear after a time limit.
In addition, tweeting with a team will prevent your writing style from being known.
Finally, Twitter can, without any given warning, delete your account. It happened with my friend Anon Watcher, and it can happen to you as well. Accounts get deleted, and then they have to come up with a new account – in short, there’s no way of recovering it.
Happy tweeting.
This article (Create a Rebellious Twitter Account and Start a Revolution) is a free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ.com.
Supporting Anonymous’ Independent & Investigative News is important to us. Please, follow us on Twitter: Follow @AnonymousNewsHQ






Great!! This is a lot of fun. Thanks! 😀
A little side note: I wouldn’t use proton mail because their servers are based in Switzerland, and Switzerland has a mutual legal assistance treaty relationship with the United States. I switched to Startmail for this reason, you can check out other options at privacytools.io