
Will Lenovo ever learn that we don’t want all of their software? Just 2 years ago, the Chinese company (Lenovo), has been banned from supplying their equipment to the networks of intelligence and even the defense services all over the globe. This has been issued by hacking as well as spying concerns brought upon Lenovo.
During the beginning of this year, Lenovo was again caught producing and marketing their computers, specifically their laptops, with “Superfish Malware” pre-installed directly onto the computers OS.
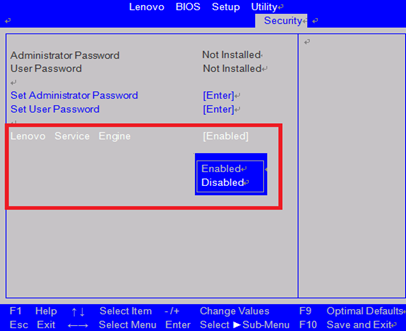
The feature in which we are talking about is known as the LSE (Lenovo Service Engine) which is actually a piece of Lenovo code that has been written directly to your computers motherboard firmware. This indicates a really hard to remove process, even for the talented. Even if you install a fresh clean version of Windows, the LSE will automatically start and install Lenovo’s software during the first boot/launch of Windows.
This issue started making reports back in May, when a person performed a full system swipe and reinstalled Windows. Since that time, online forums everywhere started to criticize Lenovo and suspicions for spying on people’s private computers.
LSE: Desktops VS Laptops;
For Desktop users, the security breach is not a high level as you may think. However, while Lenovo’s software is not sending any personal information that can identify you, it is sending basic information about your computer model/dates/time/region/and your system ID to a designated Lenovo server. Lenovo states that this only happens once, and that is during the first time setup when you connect to the internet.
Now, for the laptop users, the LSE software goes a bit further. LSE actually install another software known as OneKey Optimizer (OKO). This is a bundle in which several Lenovo laptops possess. The software OKO is intended for enhancing your computers performance by means of firmware, drivers, pre-installed app updates and even performing a scan of your computer for junk files and other common factors that can influence your computers performance.
Security researcher, Roel Schouwenberg, had reported issues about the services that included buffering overflows and even insecure network connections that was happening between Lenovo and Microsoft. This ended up as a result that actually forced Lenovo to stop installing LSE on new systems from June on forward. Lenovo also had to provide a firmware updates for the vulnerable computers, specifically laptops, and even provide the consumers with instructions on how to disable this option on the infected machines, and then clean the LSE files.
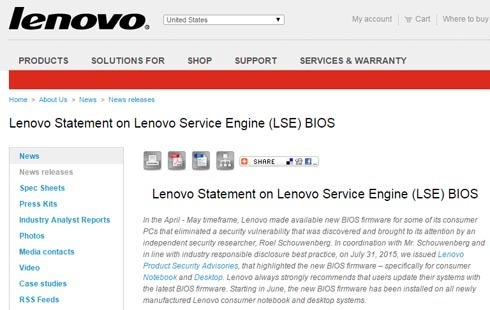
The more popular models such as Flex, Yoga Machines that are utilizing Microsoft’s Windows 7, 8, and 8.1 are reported infected with this issue. There is a full list of infected machines that you can find from Lenovo’s website.

The most effective way to remove this LSE on affected machines is to perform the action manually…What fun, I know. If you follow the simple steps below, you will be okay.
*Know which type of system you are using (32-bit or 64-bit)
*Browse the Lenovo Security Advisor and select your Lenovo Machine
*Then click on the “Date” button for Lenovo’s most recent updates
*Now you search for “Lenovo LSE Windows disabler tool” and download it.
*Once the program is downloaded, simply open it and the software will remove the LSE software from your computer.
Another alternative to this, Install Linux and replace Windows completely. There have been no known reports of LSE operating on Linux based Lenovo desktops or laptops.
This Article (Lenovo Still Using RootKit for Software) is free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ.com.





This is old news, and Lenovo have already released a removal tool for it.
The claim that it is not removable is ridiculous and not true.
“The most effective way to remove this LSE on affected machines is to perform the action manually…What fun, I know. If you follow the simple steps below, you will be okay.
*Know which type of system you are using (32-bit or 64-bit)
*Browse the Lenovo Security Advisor and select your Lenovo Machine
*Then click on the “Date” button for Lenovo’s most recent updates
*Now you search for “Lenovo LSE Windows disabler tool” and download it.
*Once the program is downloaded, simply open it and the software will remove the LSE software from your computer.
Another alternative to this, Install Linux and replace Windows completely. There have been no known reports of LSE operating on Linux based Lenovo desktops or laptops.”
pls read the article before you post.