
Lately, I have covered penetration-testing based operating systems, such as Kali Linux 2.0, as well as BackTrack 5 R3. I have also discussed security-based operating system, Qubes OS. However, there is an operating system out there that appears to combine the best aspects of both operating systems, named the Parrot Operating System.
Parrot OS provides the security and privacy that natural hackers yearn for. At the same time, it is still powerful enough, and packed full of toys to play around with. It also performs penetration-testing within the Cloud, too.
But does the entire operating system fit into a specific cloud service model? There are three cloud-based service modules to consider.
- Infrastructure as a Service (IaaS): This is when the provider supplies their own hardware and networking connectivity. The tenant will be responsible for the virtual machine itself, as well as the software stack in which it operates in.
- Platform as a Service (PaaS): In this case, the tenant will supply the web, as well as any databases needed to deploy to the Cloud. The provider will then supply anything else required to fully run the tenant’s application properly.
- Software as a Service (SaaS): This falls into the last category of the provider supplying the application, as well as the component deemed fit for the targeted operation. SaaS is a quick fix operation for the tenant.
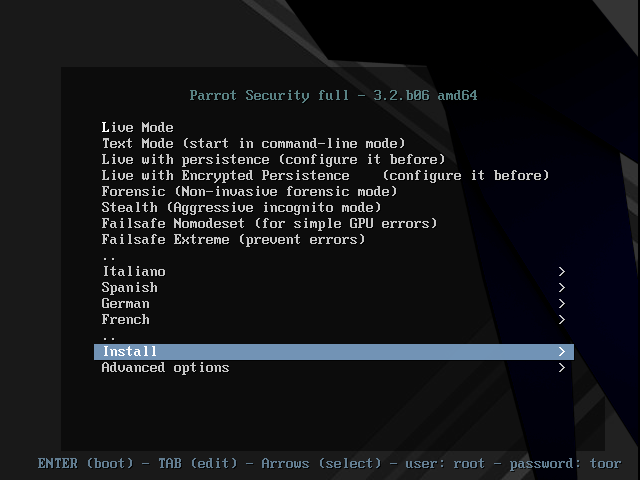
In the above screen shot, several options are there to choose from after we boot from our CD/DVD/USB drive. We can perform a live test, as well as installation. This menu also allows you to change the language to better fit your native language.
During the installation of Parrot, almost an exact replica of Kali Linux appears; the two operating systems are extremely similar in comparison, for the installation.
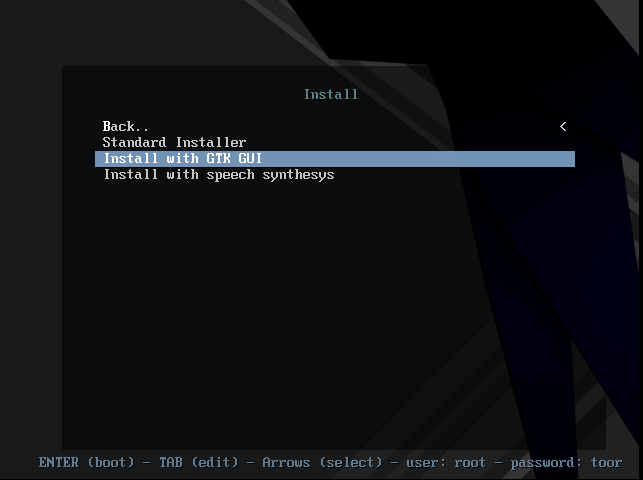
During this section of the installation, we can choose how we want to install our new operating system. Our basic choices are Standard Installer; Install with GTK GUI; and Install with Speech Synthesys.
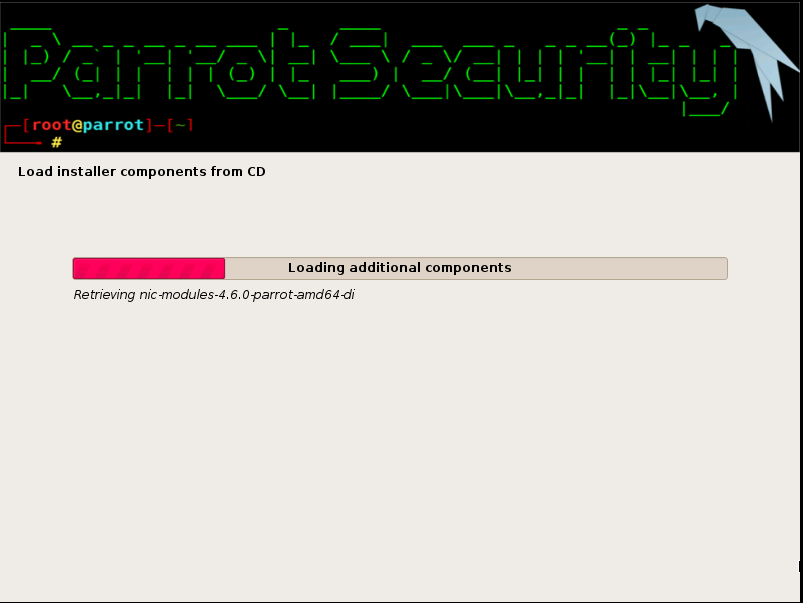
Once we have configured our language packages and basic settings, the operating system is now installing onto our device. The login screen provides us with a very slick login GUI format.
Once logged in, the first thing that any hacker would want to do is check out the toys it comes with.

As a programmer, I wanted to look into the programming field just to see what was there. Sure enough, the hackable HTML editor (Atom) is there, as well as other amazing packages, such as Arduino IDE, GRC and PyCrust.

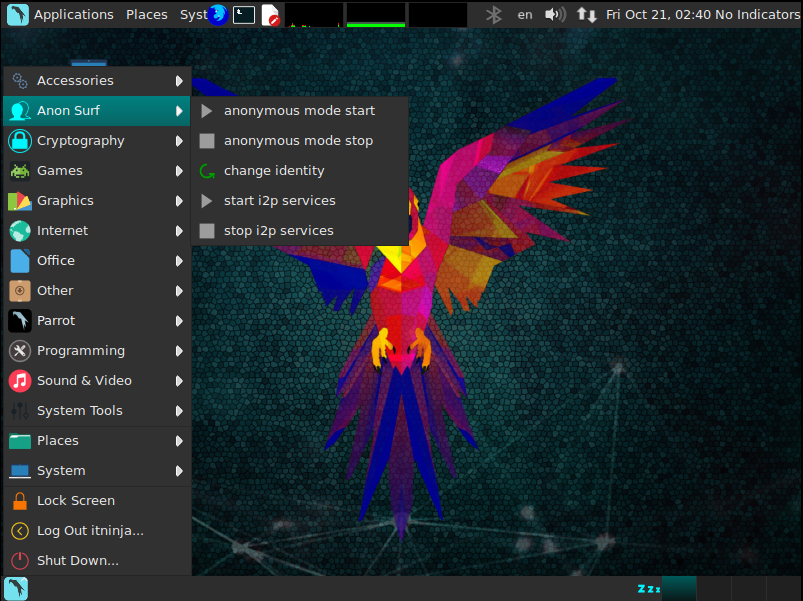
For privacy issues, I noticed right off the bat that there is a pre-installed “Anon Surf” ready to be launched. No need to configure your own VPN packages for this operating system.
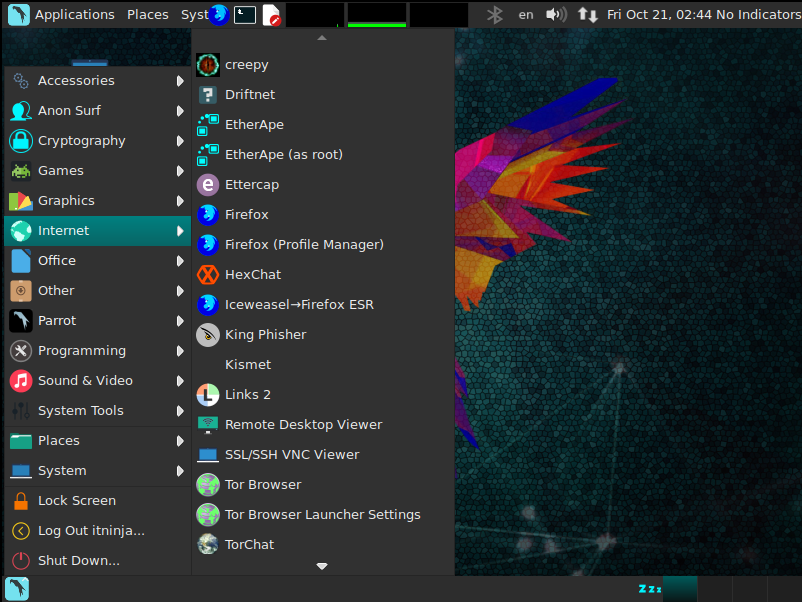
While having Anon Surf is an excellent way to remain anonymous while surfing online, this would also have to accompany an excellent browser. Outside of Creepy, Ettercap and Firefox, we also have theTor Browser already installed and ready to go. Alongside Tor, we have Tor Chat to help us remain anonymous while chatting with friends.
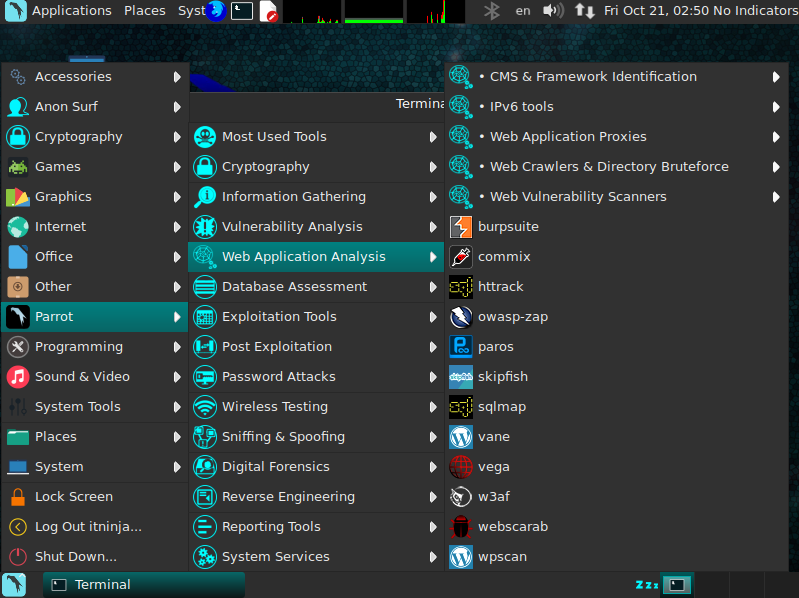
The list of applications and how to use this new secured penetration cloud-based operating system is rather long. Other interesting tools include Burp Suit, OphCrack, w3af, Wireshark, John the Ripper, WPScan, among others.
Don’t just take my word for it. Give it a test run for yourself. Let me know what you think about these operating systems. Which is your preferred choice?
You can download a copy of Parrot from here.
Sources: AnonHQ (Kali Linux 2.0), AnonHQ (BackTrack 5 R3), AnonHQ (Qubes OS), Parrot Project.
This article (Parrot OS – Linux-Based Pen Testing in the Cloud) is a free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ.





Before I delve into the overview, I strongly recommend my monster vape package for the best results.
With this gig, you will receive backlinks from:
very powerful vape blogs (DA 40 to DA70)
Profile and post backlinks on ‘000s of popular forums
Backlinks from a large network of PBN sites, wiki links, blog comments, forum posts & MUCH MORE!
Guest post links on very powerful vape-related sites.
Indexing with the search engines.
Currently, most of the big search engines are once again placing importance on the website domain authority, trust flow and other metrics. Today, if you want to rank your vape shop, you need to build up your domain authority. The only way to do this is via the creation of niche-relevant backlinks on authority sites. With this package, I will provide you with a perfect mix of follow and no follow links, a safe anchor text ratio to avoid over-optimisation and much more. I have been doing SEO for vape shops and CBD sites for over 5 years and so I know the formula for perfect rankings.
All I need from you is your website and up to 50 keywords you would like to rank for!
https://www.fiverr.com/alecmonopoly/create-a-complete-vape-shop-seo-and-backlinks-package