
It is always better to use extra security features when they are available to you. So you should know about, and use, some of the tools available to you regarding Gmail which I will lay out in this article. But that is not all, you should also increase your ‘scam-savvy’ intelligence in order to spot malware-filled scams. If you do both, then your account will be as safe as is currently possible. Follow these easy steps below:
Image Source: Google Image – 2-step verification process page
The 2-Step Verification Process
This is a magic combination against hacking. Thanks to Google for introducing the security feature that is the ‘2-step verification process’. To state this as simply as possible, this is an extra layer of security whereby when an attempt is made to log into your Gmail account from an ‘unrecognized’ PC, Google will send a code to your registered cell number on your Gmail account which you will have to enter to gain access. After doing it once on a PC, you will have the option to ‘remember this PC’ so you don’t have to enter it EVERY time. Thus making it practically impossible for anyone to hack into anybody else’s account.
Setting it up: You need to visit the setup page and follow the instructions by clicking on this link (https://accounts.google.com/b/0/SmsAuthConfig). NOTE: you need to be logged in to your Google/Gmail account first.
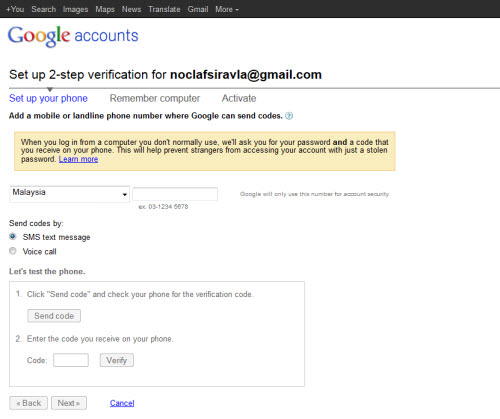
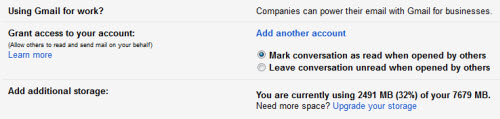 Image Source: Google Image – A screenshot of ‘Grant Access’ settings
Image Source: Google Image – A screenshot of ‘Grant Access’ settings
Check the “Granted Access” Settings in Your Account(s)
This feature is a really important one. This setting allows a different account/user access to your account and allows them to compose and reply to emails on your behalf. Why is this dangerous? If a hacker gets a chance to infiltrate your account, he will probably add his own fake mailing account into your Gmail for a faster and easier future access. Alternatively, if a hacker breaks into the account of a person you’ve ‘authorized’ on your account, it makes it easier for them to get into your account.
Setting it up: Here is what you need to do, click on the ‘gear’ icon and in the drop down menu select ‘Settings’ then go to ‘Accounts and Imports,’ from there find ‘Grant access to your account’ then remove any suspicious accounts, if present.
Also make sure the option to ‘Mark conversations as read when opened by others’ is checked. Why? When someone reads your emails without your authorization, you will know about it.
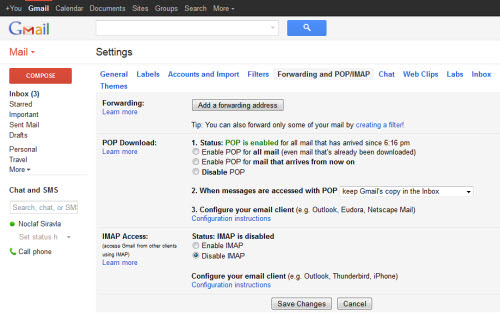
Image Source: Google Image – Forwarding & POP/IMAP setup page
Check the Filters and POP/IMAP
Back in the days when hacking was ‘easy’, the Gmail account of a very famous designer was hacked (I am not going to name him). The hacking started when the user logged into their account and then went to an infected site. The site obviously added a backdoor to their Gmail account, and to be precise, the backdoor was a ‘filter’.
Setting it up: Click on the ‘gear’ icon and go to ‘Settings’ > ‘Filters’ and delete any filters you did not create. Also, check under the ‘Forwarding and POP/IMAP’ and disable any email services you are not using. For instance, if you don’t use Outlook (or similar client) to retrieve your Gmail emails then you don’t need POP enabled.
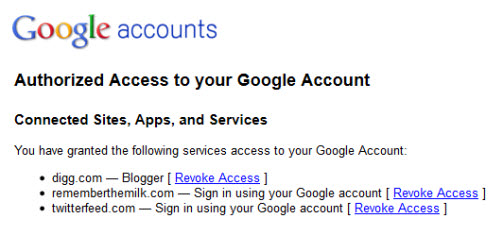
Image Source: Google Image – Screenshot of Authorized Access controls
Stop Unauthorized Access
There are web applications or websites that give you the option to ‘sign in using your Gmail’, Twitter, Facebook, so on and so forth… this is one of the best tricks to gain access to your Google account. Many people ignore this loop hole, as the option is promoted by Gmail itself.
Setting it up: Click on the ‘gear’ icon and then ‘Settings’ > ‘Accounts and import’ > ‘Other Google account settings’. From there, go to the ‘Connected apps and services’ heading and click ‘Account permissions’… if you think there are any doubtful applications within the list, then simply ‘revoke’ it.
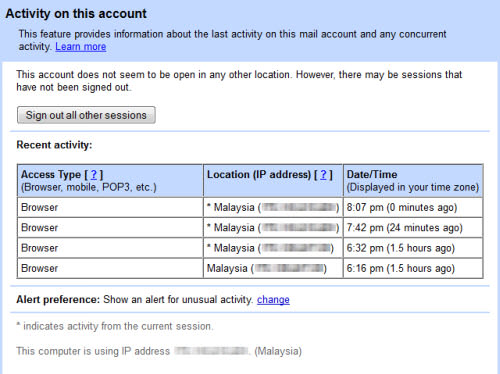
Image Source: Google Image – Screenshot of ‘Account Activity’ page
Tracking Account Activity
The best way to keep an eye on your account is to constantly check your account on a regular basis. The best way of doing that is to know about your account’s activity. Gmail has created a security feature in the ‘Activity Information Panel’ which allows you to track various activities on the account.
How do I go there: Log in to your Gmail account and at the bottom right of your mail, you should see a message saying, “Last account activity: X minutes/hours ago.” Click on the ‘Details’ link underneath that and you will be able to see the access type, location and date that you have viewed your Gmail account in the recent past.
Image Source: WOT – A screenshot of WOT website
Install a Security Plug-in(s)
No matter how strong you set up the security on your Gmail (or any other) account, you might become prey for a hacker through their scam emails or applications. To fight these tricks you can install browser plug-ins. These plug-ins are programmed to recognize phishing sites and remove possible threats.
Try ‘Web of Trust’ (or WOT). It simply shows website reputations as traffic lights next to search results when you use Google, Yahoo!, Bing or any other search engine. Icons are also visible next to links in social networking sites, like Facebook and Twitter, and email services, like Gmail and Yahoo! Mail, as well as other popular sites like Wikipedia. By clicking the traffic light icon you can find out more information about a website’s reputation and other users’ opinions. A green traffic light means users have rated the site as trusted and reliable, red warns about potential threats and yellow indicates that you need to be cautious when using a site.
Image Source: Google Image – Screenshot of Gmail login page
Create a Tough Password
If you have enabled ‘2-step verification’, your password is the only thing that is an access layer between the hacker and your private emails, contacts, and financial details. In order to make your Gmail more ‘un-hackable’, you need to create a password that would be (virtually) unbreakable.
- Create a password that is not available in the dictionary.
- Add numbers to the base-word to make it more secure.
- Use punctuation and symbols to complicate it more.
Add more complexity by adding upper and lowercase letters.
SOURCES:
https://www.google.com/safetycenter/families/start/
http://www.latesthackingnews.com/2015/01/18/4-ways-secure-g-mail-account/
http://www.huffingtonpost.com/robert-siciliano/10-ways-to-protect-your-g_b_5458850.html
http://blog.kaspersky.com/4-ways-to-secure-your-gmail-account/
https://support.google.com/mail/checklist/2986618?hl=en
http://46qasb3uw5yn639ko4bz2ptr8u.wpengine.netdna-cdn.com/files/2012/11/gmail-logo.jpg
https://chrome.google.com/webstore/detail/wot/bhmmomiinigofkjcapegjjndpbikblnp
https://www.mywot.com/en/download
https://support.google.com/mail/answer/3070163?hl=en
https://support.google.com/mail/answer/45938?hl=en
https://support.google.com/mail/answer/41078?hl=en





I don’t believe in a annonymous. Hack this computer Im on leaving stupid remarks, and I’ll have faith.
i salute u all for creating a site and a group who will standup and tell the world like it is.go fourth and multiply my friends.