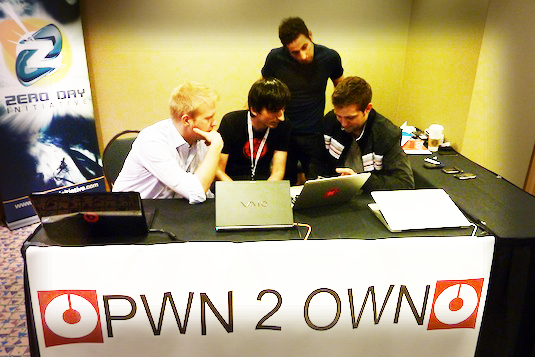
Jung Hoon Lee was the day’s most valuable player, netting the single-largest payout in Pwn2Own history, for an exploit that altered both the stable and beta versions of Google Chrome. He brought in approximately $916/second for his two minute demonstration.
Lee leveraged a buffer overflow exploit in Chrome, he then used an information leak exploit in two Windows kernel drivers to obtain full ‘SYSTEM’ access. He also managed to exploit the 64-bit version of Internet Explorer 11, with a time-of-check to time-of-use (TOCTOU) vulnerability allowing for read/write privileges.
“He evaded all the defensive mechanisms with a sandbox escape through a JavaScript injection, all of which resulted in medium-integrity code execution,” says HP’s Dustin Childs, in his recap.
However, he wasn’t finished wreaking havoc. He additionally pwned Apple Safari by means of a use-after-free (UAF) vulnerability in an uninitialized stack pointer in the browser, and avoided the sandbox for code execution.
Another hacker, going by ‘ilxu1a,’ used an out-of-bounds read/write vulnerability resulting in medium-integrity code execution in FireFox. He brought in $15,000 for his findings.
“It happened so fast that those folks who blinked, missed it… although in our defense, it was a sub-second execution,” said Childs. He reports he discovered the bug through ‘static analysis,’ which is really remarkable.
ilxu1a additionally tried to show off another exploit in Google Chrome, but ran out of time.
“As with every Pwn2Own, all vulnerabilities were revealed to their various respective vendors in our Chamber of Disclosures, and each seller is working to fix these bugs through their own procedures,” Childs said.
SOURCE:
“Pwn2Own Sees All Major Browsers Fall.” Infosecurity Magazine. N.p., 23 Mar. 2015. Web. 24 Mar. 2015. http://www.infosecurity-magazine.com/news/pwn2own-sees-all-major-browsers/




