For several online casinos, their business usually peaks as their online gambler’s come home from work and log into their favorite Blackjack tables or Texas HoldEm. However, on Tuesday February around 5:00PM the house did not favor the odds. This particular casino that has tens of millions of dollars in virtual transaction data, several thousands of gamblers profiles, and even more millions that has been invested into the infrastructure was hit with a ransomware that had brought a very thriving online company to a directly encrypted cyber-crime scene.

The master-mind criminals behind the direct attack could have not asked for a better target. The, legal, online casino that is located outside of the United States, just happens to be one of a few of the largest operations in the field of online gambling and other entertainment business. However, the casino wishes to remain anonymous for the safety of their organization, as well as the protection of their users; they were provided with an extremely rare taste of high-stakes ransomware attacks that had served as a cautionary story for any company.
While ransomware was on their radar, the business, in which uptime is very crucial for their success; DDoS attacks as well as APT attacks had always been upon their brink of security concerns. To be on the clearer side, the casino had invested extensively in security protocols that where in place, and other tools, in order to aid in the protection of their network.
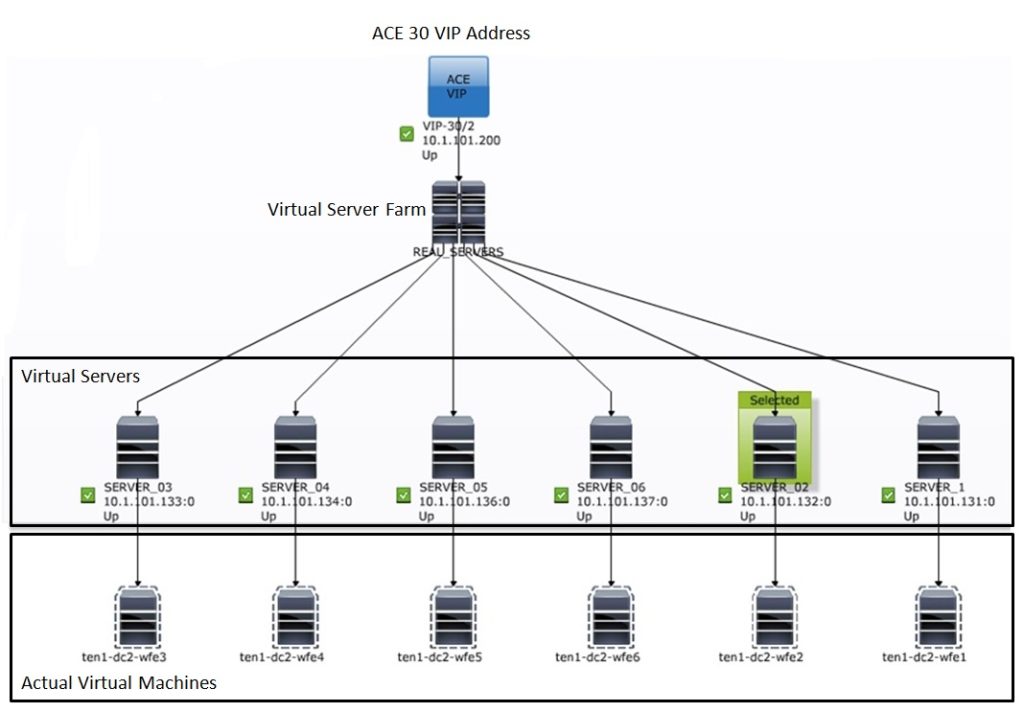
This casino, in which holds 1,000 employees, possess two extremely large infrastructure data centers, and also a large cloud infrastructure. Relying on heavy security, the casino utilizes a firewall from a reputable top-tier supplier. The data center security comes from that of another leading vendor and possess the clients AV (Antivirus) protection from a mixture of other leading providers. This was also contracted to operate in a real-time network in order to perform the correct monitoring from yet another outside service provider.
Needless to say, I believe it would be considered an understatement, if someone said that security was of their top concern. Protecting thousands of user’s data, as well as the casino’s infrastructures as well as revenue, is of their utmost concern.
However, with that being stated, there are no perfect security solutions, and on that Tuesday evening, as their usual gamblers were logging on, their servers whirled and then spun into a massive overdrive. This casino soon learnt in the most extreme way, that nothing is bulletproof.
The attack of the ransomware started a 5:00PM with the starting point of the hook from a simple Phishing email, which possess a bogus invoice that had been sent to another external consultant working in-house. While the software was working just behind the casino’s firewall onsite, the consultant had received an email in which had a subject line was “Requested Receipt ID: 084C9F.” The consultant paid no attention to the email, and didn’t suspect anything wrong with the email, or the emails attachment that had been labeled as “segreteriagenerale_request_084C9F.zip.js.”
In this section, “JS” of the attachment’s extension was obfuscated by the attacker. And naturally, the JavaScript was that of a malicious attachment.
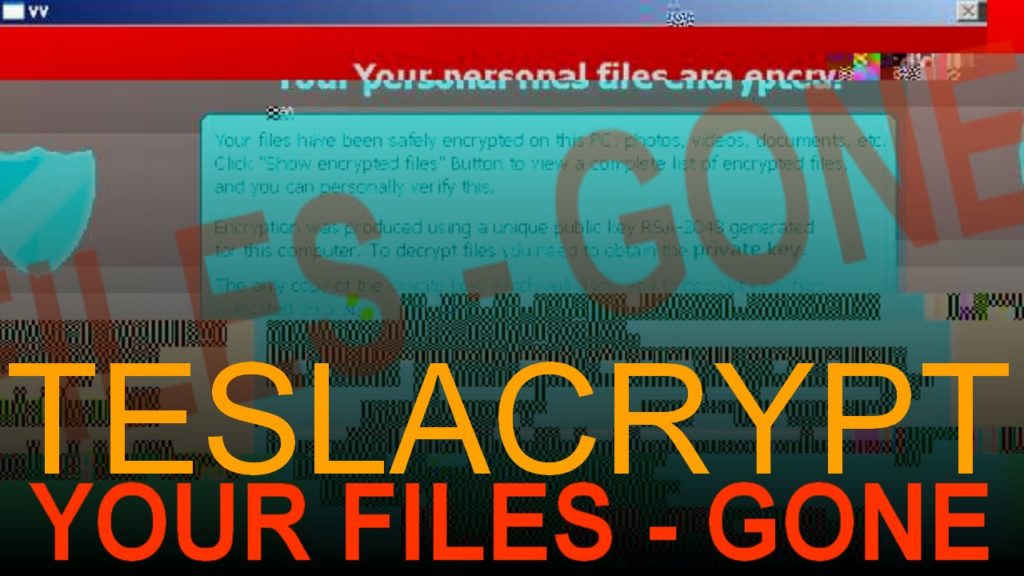
However, in this case, the payload was in fact the “TeslaCrypt 3” ransomware.
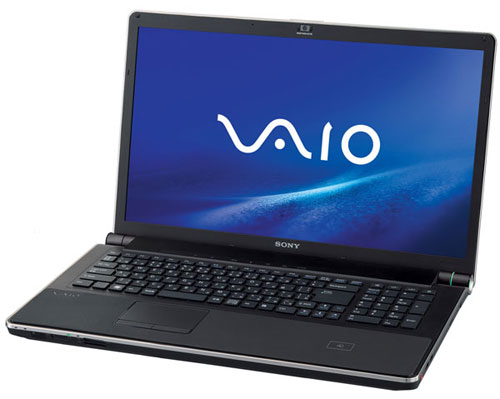
Utilizing a Windows 7 Sony Laptop, that was bestowed to him by the casino, the consultant proceeded to open the email message and even double-clicked the email’s attachment, thus, leading onward to unleashing the horrifying ransomware. Completely unaware by the casino, was the fact that their consultant’s laptop did not possess any security software to aid in preventing this from happening. Moreover, making things even worse for the company, the consultant’s laptop was also misconfigured with a “C:\Users\username\Public” folder that had been wrongly setup, to be completely shared across the casino’s network.
With this small unprotected laptop, the ransomware had completely attacked the notebooks default “My Folders” directory and then proceeded onto encrypting those files. This only took a matter of minutes. The consultant had noticed that he was unable to open any of the documents he had just created, and that they had new extensions that included: .XXX, .TTT, and .MICRO, which had been appended onto those documents.
Concerned about the technical issues, he called the casino’s IT department for answers. While awaiting the phone call, he searched for answers on his own in Google. After a half-hour of waiting, the IT department finally contacted him and instructed him to unplug his Ethernet cord as fast as he could.
The laptop belonging to the consultant was also linked to another 80 desktops and laptop computers. All of which were linked by a network of another 15 shared servers within the casino’s operations. The servers had contained a full mixture of critical network elements that consisted of the companies Active Directory Domain Services, and even the companies treasure trove of several applications and valuable data.
Within just 60 minutes, the casino’s 3rd party security firm, that was based in London, DarkTrace, had not only received information that the casino was dealing with a massive ransomware attack, but had already detected it before the cyber security firm did. The casino’s network, end points and the traffic were busting open with odd behavior.
During the hour of damage, the casino thought that the ransomware had been contained strictly to the laptop, in which was by now quarantined from the rest of the network. The damage that had been emitted from the TeslaCrypt 3 had also infected the primary laptop of the consultant files within the “C:\Users\username\Public” folder. However, the casino could not have been any further from the truth.
While the casino’s IT team performed a local triage, the DarkTrace technicians noticed something bigger. DarkTrace noticed a tsunami of network activities, as well as anomalies within the casino’s network.

Dave Palmer, a director of technology working for DarkTrace, stated that they were watching the ransomware work its way through the network and scanning the file directories in an alphabetical order. They had spotted the unusual network traffic and the executables zipping around the casino’s network at lightning fast speeds. This caused a massive spike inside the number of files that were being touched. The failed password attempts went off the charts; they were also seeing traffic coming into the network from other outside domains – such domains that no one from the company had even visited before.
Impressively, the ransomware had worked its way into the Hitachi shared storage server from inside the consultants main public file “C:\Users\username\Public” folder.
Now, time is extremely crucial for this thriving online casino, and this attack is not the kind in which you engulf yourself into a cup of coffee while you work on the situation at hand. Both DarkTrace, as well as the casino’s IT division where working fast, in order to cordon the ransomware, and ultimately prevent it from infected the rest of the server and limiting the TeslaCrypt 3’s ability to encrypt even more endpoints.
However, the casino’s nightmare is not completely unique on its own. There has been other reports of similar incidents of a successful “CryptoWall”, “TeslaCrypt”, “Pyta”, and even “Locky” ransomware attacks that are steadily on the rise of cyber-crime activities. Top security researchers at Cisco Talos has informed the public that they are seeing a large spike that is targeting attacks on hospitals as well as other niche industries that leads from spear phishing and other forms of spam attacks.
As we look at past attempts of non-ransomware attacks, they happen cautiously and quietly. However, ransomware is just the opposite. The main goal of a ransomware infection is to strategically grasp a stranglehold on the respective organization as quickly as it possibly can. Then it goes on a hunt. It hunts down and proceeds to encrypt as many files as possible, while utilizing as much of the organizations bandwidth as possible.
For the cyber-defense company, DarkTrace, the casino’s ransomware was just a typical attack. Typically, other companies utilize a temp, contractor, and other suppliers such as 3rd party services in which they are plugged into a gap. Loaner laptops from companies are seldom operating on recent operating systems and fail to have all of the patches up-to-date.
To prevent this from occuring again, the company is now double checking the correct access privileges on every computer and server, while exercising extreme discretion when the time comes for others to have any access into the back end. The casino is also spending more time on educating their employees and informing them on how to spot “Phishing” emails.
**Please download a PDF Version of this article for future offline reading HERE**
Sources: ThreatPost, BleepingComputer ,Windows 7, DarkTrace.
This article (Ransomware Attacks Online Casino) is a free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ.





OK any ideas which casino this is??