Hello hacktivists. I am sure that by now, we are all aware that the BackTrack Linux is a repository of Kali Linux. You may have already read my previous article about Kali Linux 2.0, in which discusses the latest update (of that time) for Kali Linux. Kali Linux is globally known as the “Hackers Operating System.”
BackTrack is no different. This operating system is another security focused based Linux system, and like Kali, it is crammed pack with the best free-based software needed to perform extensive penetration testing. BackTrack is also piggy-backed off of the Ubuntu Desktop. The latest version has been dubbed “Revolution.” Revolution is the latest version of BackTrack 5 R3 and was released just a few short days ago. And I just could not let this version slip away without installing it myself.
This version of distribution had been designed to appear for penetration testers, as well as other respective security professionals alike. This operating system is also ideal for those who are interested in messing around with some of the best security tools on the market that have been provided by the hacktivist community.
Now, for the average computer user, this isn’t the type of operating system to install just to simply check their email accounts and social media. Saying that, this operating system has been made publicly available, for direct download as a DVD installation image, supporting both 32 and 64 Bit architectures. Even better, there are installation images based upon the KDE, as well as the Gnome environments.
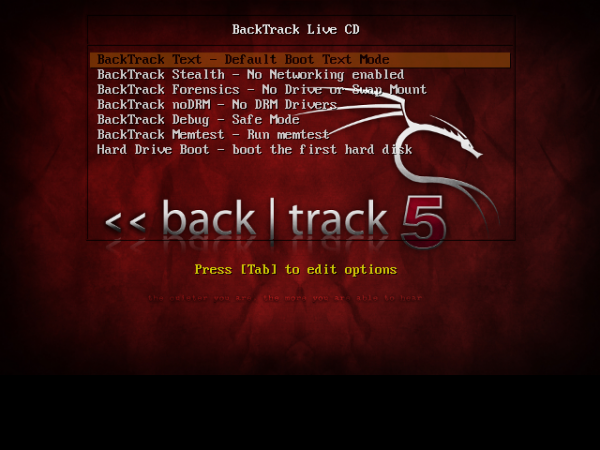
Unlike in the past, with traditional Linux-based operating systems, BackTrack 5 R3 boots into a console-based environment. If one would like to initiate the graphical interface of BackTrack 5 R3, you would type in “startx” and then press Enter. This same method proves to be true even after the installation of your new hackers operating system. Typically, the system will boot into a type of login section. Just like the Kali Linux, our default login user name is “root” and the password is “toor”. However, the password can be changed during the installation process to that of which you choose. And yes, if you are wondering if the same login applies to KDE and Gnome, the answer is yes it does.
Due to the operating system being based off Ubuntu Desktop, the installation of BackTrack 5 R3 is almost identical to the Ubuntu’s installation guide. However, the latest edition utilizes an older form of Ubuntu Desktop environment. In essence, BackTrack 5 is based on the Ubuntu Desktop 10.04 LTS module.
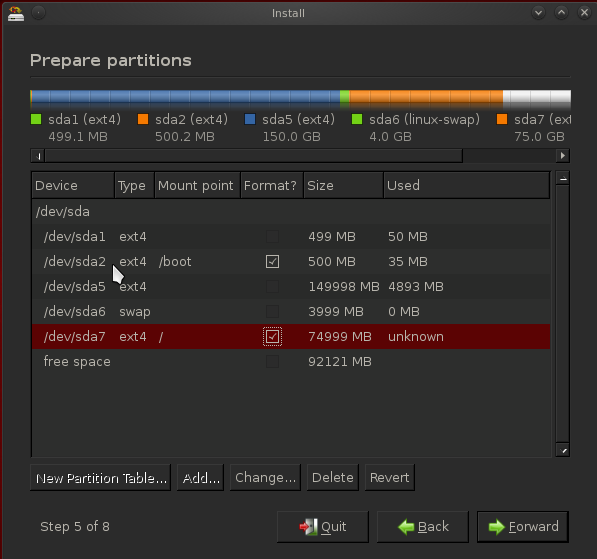
While I was installing my copy of BackTrack 5 R3, it seems to be merely impossible to install the operating system’s boot loader on a separate partition, while trying to create a dual boot system that already hosts another distribution or operating system. So, I ended up installing my copy onto a Virtual Machine.
You can see a screen shot of the “Advanced Partitioning Tool” of the operating systems KDE version.
One can also utilize BackTrack to perform simple computing activities of day-to-day lives, even though this O.S. was not initially designed and built for that purpose. Mozilla FireFox, for example, comes preinstalled with the ‘Out-of-Box’ version; you can utilize the browser to start surfing the Internet right away. BackTrack 5 R3 also comes with the latest edition of FireFox (Firefox 14), which is also installed into this build.
The developers of this have also taken the security issues extremely seriously. So much so, the FireFox that is pre-installed, comes with pre-loaded addons to provide another layer of security while surfing the net.
Almost every single application that is preinstalled for this operating system is designed specifically for penetration testing purposes, however, instead of going through the never-ending list of amazing tools that come with this O.S., I have chosen to take screen shots.
**Please note, these screen shots are based upon the KDE version I’ve installed**
The screen shot below shows the menu opened up with Information Gathering -> Wireless Analysis -> WLAN Analyses Categories.

This screen shot is Vulnerability Assessment -> Network Assessment -> VoIP Fuzzers

While looking into the Applications that are nested inside the Exploitation Tools -> Physical Exploitation category, a nice list of software tools for physically exploiting different hardware devices, is displayed. Some of these applications are new to BackTrack 5, making their first appearance.

Here, you can see a list of software programs inside of the Privilege Escalation -> Spoofing Attacks -> VoIP Spoofing.

Here are the applications nested inside of the Maintaining Access -> OS Backdoors category.

Naturally, we still have our Reverse Engineering tools!

This screen shot below references our tools that can be found in the RFID Tools -> RFID Frosch.

Our applications for Network Stress Testing.

We also have applications nested in the Forensics -> Forensic Analyses Tools section.

While this was intended for the respective user to have more than just a simple passing knowledge of managing the navigation of a typical Linux system, you can still find the graphical management applications normally found in regular desktop distributions, in BackTrack. From the screen shot of the KDE version, the installing and management applications may also be accomplished by means of the software manager inside the KDE’s system settings.
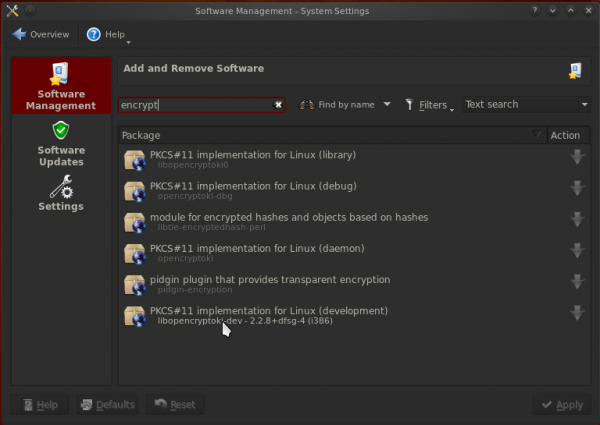
Due to the fact that BackTrack 5 is based on the kernel of Ubuntu 10.04 LTS, the same applications are also available inside the repositories of the Ubuntu edition, and can also be installed on BackTrack 5 R3, meaning you can still find those packages for OpenOffice 3.2.
If you would like to get your hands on a copy of BackTrack 5 R3, please use the links below. You can learn how to start using BackTrack 5 from here.
Download Links; (Torrents Only)
BackTrack 5 R3 Gnome 64
BackTrack 5 R3 Gnome 32
BackTrack 5 R3 KDE 64
BackTrack 5 R3 KDE 32
BackTrack 5 R3 Gnome 32 VM
Sources: AnonHQ (Kali Linux 2.0), Backtrack Linux (How To), BackTrack 5 R3 (Download Page).
This article (BackTrack 5 R3 Review) is a free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ.





So what is the difference between Kali and Btrck?
I don’t understand why you review an old OS like this in 2016 if we are already a few versions further!? Why don’t you also make a review of Windows XP? The backtrack project stopped and changed its name to Kali Linux, and we’re at version 2 now, which you could call backtrack 8 (yes 8, because of big updates in both versions) >> https://www.kali.org