Written by: Alek Hidell
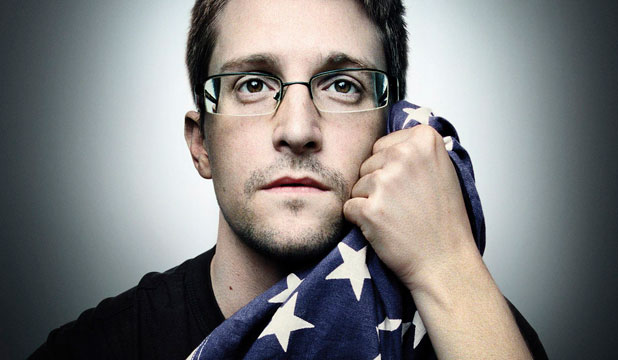
Most of the American public is probably not familiar with journalist Laura Poitras, however she played an integral role in the publication of the NSA files leaked by Edward Snowden. Snowden contacted Poitras via an anonymous email and began to provide details of the leak he was going to provide her. While Poitras was interested in meeting Snowden in person, he insisted it was not possible. It was at this point that Poitras began communicating with Snowden using a number of anonymity based software programs known as crypto tools. Crypto tools hide the user’s identity and data through encryption and typically mask the user’s IP address, in order to protect them from spying eyes.
Poitras purchased a laptop and installed Tails, an operating system which funnels all network traffic through the Tor network and leaves no communication data on your hard drive. She was able to communicate with Snowden anonymously using internet cafés and public Wi-Fi, making sure her communications could not be traced. Poitras eventually met Snowden in a Hong Kong hotel room. The purpose for their meeting? Poitras was filming a documentary about surveillance and activism, which after interviewing Edward Snowden, became Citizenfour. Citizenfour was the name Snowden used to contact Poitras in the first emails he sent to her.
According to Poitras, her communications with Snowden and the filming of her documentary would not have been possible without the use of crypto tools like Tails and Tor. “I have a lot of respect for the cypherpunk movement,” she adds. “The free software community should be supported more widely. I’m totally in solidarity with what they do.” Poitras credits several specific tools she utilized in the making of her film. The first of which is Securedrop. Securedrop is a software tool developed by the Freedom of the Press Foundation, and was originally coded by Aaron Swartz. The idea behind Securedrop is to allow whistleblowers to submit information to journalists anonymously and securely. The information is passed using the Tor network to connect private servers handled by journalists. The process also involves the use of two flash drives and a non-networked computer. For the average person, this may seem like overkill, but what does it say when knowledgeable investigative journalists have to turn to this type of security in order to protect their first amendment rights? Poitras also used GPG Encryption. GPG encryption is a form of encryption which utilizes a passcode set by the sender, which has to be entered by the reader in order to decrypt. GnuPG is a free crypto tool which you can use to send private encrypted data using a passcode. Poitras also utilized Off-the-Record Messaging. OTR Messaging is a private and encrypted messaging system which not only encrypts communications, it removes all digital signatures that could potentially identify you to a third party. The digital signatures embedded in most communications are more than sufficient to identify you to the NSA or other spying organization. Poitras had been repeatedly stopped and searched since her 2006 investigative film about Iraq, My Country, My Country, every time she re-entered the US. This prompted her to better hide her data and film footage using software encryption tool TrueCrypt. TrueCrypt uses real-time encryption, which means data is encrypted as it is written to the hard drive. TrueCrypt is available for Windows and Linux.
‘Citizenfour’: Documentary shows Snowden reunited with dancer girlfriend in Moscow
As mentioned earlier, Tor was an integral in Poitras’ work, and has become a staple in the activist community. Tor routes your data through a network of servers, bouncing your information through multiple nodes, thereby hiding the user’s IP address. Why is hiding your IP address important? Your IP is your internet home address. Many people say, “well I have nothing to hide.” That is not the point. The point is that privacy worldwide is eroding away and by hiding your IP address, not only do you protect your identity, you make a statement that invasions of privacy are not ok. Tor is the first, best, most accessible hope for internet privacy.
Poitras was one of the founders of Intercept, a new online magazine, along with journalist Glenn Greenwald. Intercept plans to focus much of it’s attention to the NSA and it’s worldwide surveillance. The goal of the magazine is to create “aggressive and independent adversarial journalism.” Definitely something we need more of in this world.
____________________________________________________________________________
Sources:
http://www.wired.com/2014/10/laura-poitras-crypto-tools-made-snowden-film-possible/
https://freedom.press/securedrop
https://en.wikipedia.org/wiki/TrueCrypt
https://otr.cypherpunks.ca/index.php
http://www.theguardian.com/media/2014/mar/02/glenn-greenwald-first-look-intercept






I relate very much to this article. I’m stuck in the middle of everything. Its bull SHIT.
very interesting
Free software are the key to everything else. It just begin by choosing GNU/Linux and free softwares over Windows and their proprietary ones. All united, we can do a lot.
Be wary about using TrueCrypt, it has been cracked by the UK & USA security services.
You would be wiser to use PGP.
No Trucrypt was taken out because there was no government backdoor only the government and super rich are allowed secrets and privacy….
Truecrypt is no longer at the website but you can get it here I have verified the file using SHA 512 I use Truecrypt to archive all my backed up blue ray and DVDs! I used Tor to leave this message!
ggpg4win is also included in the package you will have to use a proxy/VPN or Torto access Kickass Torrents
Pack contains:
Eraser
gpg4win
KeePass
MD5 SHA Checksum Utility
Tor Browser
Truecrpt
https://kickass.so/open-source-privacy-and-security-package-for-windows-t9757801.html
One small correction: You don’t actually install TAILS (The Amnesic Incognito Live System) to a computer. It is a secure linux operating system that is run from a USB drive. Because of this you can run it from any computer. You just have to boot from the USB drive.