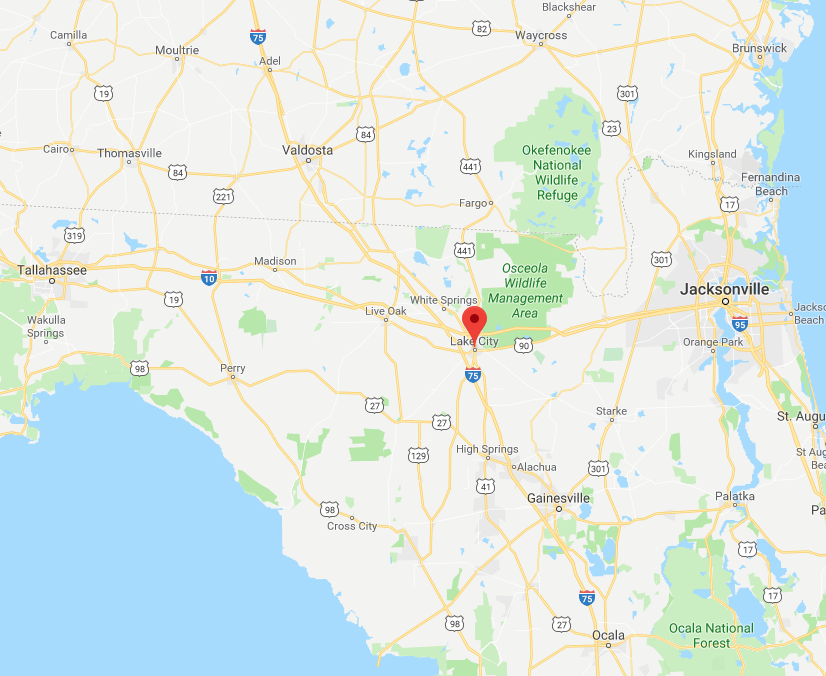
(Zero Hedge) Cyber-criminals have struck for the second week in a row, this time on a small Florida city called Lake City, according to the WSJ. The city has agreed to pay ransom to the tune of hundreds of thousands of dollars after a ransomware attack crippled its systems.
Lake City’s council approved the measure during an emergency meeting Monday night and will be paying about $462,000 via Bitcoin, by way of the city’s insurer. This payment follows a similar incident in Riviera Beach, a city of 34,000 near West Palm Beach, where the city’s council authorized a similar $600,000 ransom payment.
The event [in Lake City] began June 10 with what the city described as a “triple threat” malware attack, then escalated with a ransom demand last week, the city said in a news release. The attack knocked out email and hindered city services, and people had to temporarily pay utility bills on terminals at the police station, the city manager said. The attack included a ransomware variant called Ryuk that is known for hefty ransom demands.
Emergency services weren’t affected. But Lake City authorities worried they wouldn’t be able to access encrypted files such as ordinances, public-record requests and utility information.
These are both signs of how increasingly sophisticated hackers are targeting cities with outdated IT infrastructure and holding them ransom for sizeable sums. And suceeding. The Riviera Beach ransom was about 12 times the size of a ransom demand that Atlanta refused to pay last year. These demands are becoming more common and are growing in size. The six figure sums averaged only a couple thousand dollars a few years ago.
Ironically, the hacking measures appear to come thanks to a hack of the NSA’s own weaponized hacking arsenal, which is now being used against the US.
Larry Ponemon, whose Michigan research company, the Ponemon Institute, focuses on information security said: “There are a lot of copycats out there, and they figure they’re going to ride the gravy train.”
Attackers are going after both companies and cities regularly by exploiting vulnerabilities via malicious email attachments and demanding payments for decryption keys.
The attacks occur “every day and many are never publicized”. Local governments are especially vulnerable if they lack resources to update infrastructure and invest in security.
Michael Tanenbaum, head of North America cyber and professional liability at insurance giant Chubb said: “We do see an increased frequency against municipalities.”
The FBI advises against paying hackers, saying there’s no guarantee they will release data and that it could make victims susceptible to future attacks. But some victims don’t have a choice: for instance, in March, Jackson County, Georgia paid $400,000 after realizing a cyber attack had compromised its backups.
Joe Helfenberger, city manager in Lake City said: “I thought we had a backup, but obviously we didn’t have a good enough backup for this kind of attack. Fortunately, we had all the financial data backed up properly off-site, so that wasn’t affected, but pretty much everything else was.”
The payouts are emboldening hackers to raise their demands. Ponemon said: “That might explain why the ransom is going up: The bad guys can get away with it.”
At the start of this month, we detailed a similar ransomware attack on the City of Baltimore. Officials have estimated that attack, where Baltimore rejected a $76,000 ransom, will instead cost the city about $18 million in IT costs and lost revenue.