
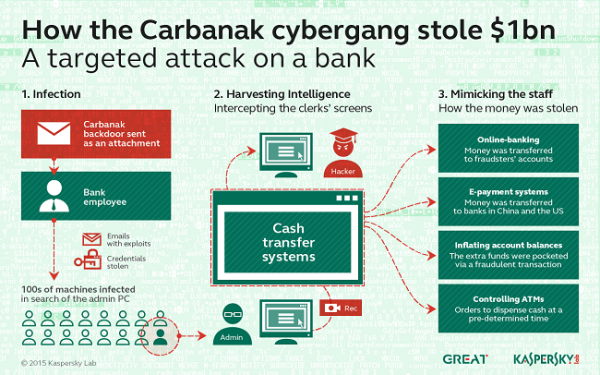
Image Source: Kaspersky – An infrastructure of Carbanak backdoor RAT software being described as it can infiltrate via an email.
Since 2013, a group of hackers have been planting malware into several banks around the world. To be precise, they have been planting them in their internal computers used by employees who process daily transactions and keep detailed financial records.
The software that was planted into the systems then replicates itself onto several other computers on the network and sends back video feeds and images. This led to the hackers impersonating bank personnel and hacking other cash machines, all said and done, they were able to transfer millions of dollars from Russian, Japanese, Swiss and American banks into dummy accounts created in those respective countries.
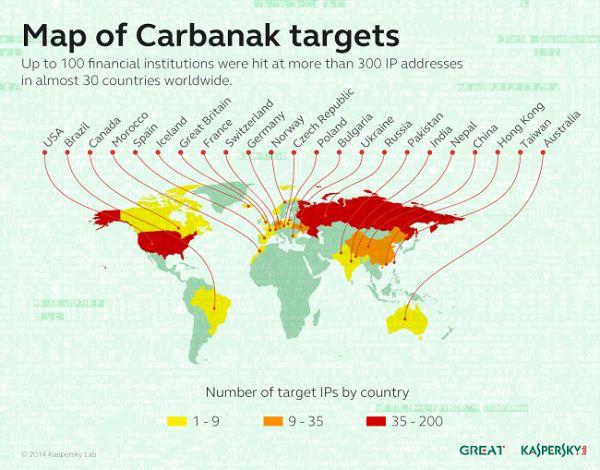
Image Source: Kaspersky – Up to 100 financial institutions were hit at more than 300 IP addresses in almost 30 different companies, worldwide.
“Hackers send [an] email containing a malware program called Carbanak to hundreds of bank employees hoping to infect a bank’s administrative computer,” Chris Doggett, manager of Kaspersky’s North American office in Boston.
For those few, when the time was right to cash out their three years of hard work, the hackers used online banking or international electronic payment systems to transfer money from bank accounts to their own. The stolen mint was deposited with banks in the United States or the Republic of China. The investigators are not sure if any other banks in other countries were used as receivers too.
#Hackers rob #globalbanks for more than 100 #milliondollars. This is the most sophisticated and largest #heist ever.
— Anon.Dos (@anondos_) February 15, 2015
Apart from just this, they penetrated deeply into every accounting system, inflating account balances before pocketing the extra funds via many false transactions. For instance, if an account had ten thousand dollars, the hacker would change the value to twenty thousand dollars and then transfer ten thousand to their accounts. In doing this, the original account holder does not suspect anything is amiss because the original ten thousand dollars are still in their account.
“We found that many banks only check the accounts every ten hours or so. So in the interim, you could change the numbers and transfer the money,” Mr. Golovanov, of Kaspersky Labs, said.
Furthermore, the hackers were able to control the banks’ ATMs and they would program them to spit bulk chunks of cash at a precise time. When the program was executed, a team member would be waiting right next to the machine to collect ‘their’ money.
Image Source: Kaspersky – Indirect attributes of Carbanak’s presence in a bank network. A Paexec file in windows\catalogue heling to run commands on a remote machine. 1) There are files with .bin extension at the following location: \All users|%AppData%\Mozilla\ or c:\ProgramData Mozilla\. 2) There is a svchost.exe file in Windows\System32\com\catalogue or Windows\Systemwow64\com\catalogue (for 64 bit OS Windows). 3) Among the active Windows services, the services ending in “sys” were found, duplicating a similar service stored without the “sys”.
“These bank heists were surprising because it made no difference to the criminals what software the banks were using. So, even if its software is unique, a bank cannot get complacent,” said Sergey Golovanov, Principal Security Researcher at Kaspersky Lab’s Global Research and Analysis Team. “The attackers did not even need to hack into the banks’ services: once they got into the network, they learned how to hide their malicious plot behind legitimate actions. It was a very slick and professional cyber-robbery.”
“Second best way is to impersonate the person that owns one. Sounds like what these guys did. However, according to TFA they were very patient and methodical, leading up to the assertion that they were ‘cybercriminals’ rather than state actors. Of course, the last time this weird dichotomy came up, the attackers were state actors because they were so patient and thus weren’t plain ol’ criminals. Sounds a bit clueless to me. Given the level of information we get from fine articles such as this, I have to wonder just what, if anything at all, really happened,” says Roger Golub, Computer World.
Anonymous recommends: Protect your PC & mobile devices from hackers & governments & surf anonymously
SOURCES:
http://www.theverge.com/2015/2/14/8039593/hackers-malware-robbery-millions-bank-heist
http://en.wikipedia.org/wiki/Carbanak






…
These guys are legends!
I couldnt see wich group of Hackers did this Operation? is there any information?
thanks
is there any info about the group name of hackers?
Dang, niceeeee.
Good Shit……
Real enough to fool the fool…Intuition says a plot by big banks or Banks to get whatever federal agency on there side of the internet security, privacy and their interest money. If it sounds to good to be true it probably isn’t.