
The strength of Apple’s iMessage end-to-end encryption has been tested by whitehat hackers who, in 2013, figured out the method behind it and revealed that Apple controls the encryption key base and could, thus, be forced by court order to turn over messages.
Apple’s current CEO, Tim Cook, denied these charges last September at a conference, but in any case, trust in the security of messages being sent over iMessage has not been 100% since.
Enter Moxie Marlinspike, a computer security researcher, and his company Open Whisper Systems, who have released version 2.0 of the free ‘Signal’ application for Apple iOS — now including end-to-end SMS/MMS encryption along with encrypted phone calls, which were presented last July with Signal 1.0.
Signal 2.0 adds #encrypted #messaging to the encrypted voice calling that was introduced last year.#Apple #AppStore pic.twitter.com/oHauZoAOvp
— Anon.Dos (@anondos_) April 21, 2015
This safe messaging platform for iPhone is free and open source, and it is indeed not the last venture for Marlinspike — who is also the head of ‘Red Phone,’ an application that encrypts voice calls for Android, as well as ‘Text Secure.’
However, unlike Red Phone and Text Secure, Signal 2.0 has both encrypted SMS and voice calls in one place. The company is also planning to release a desktop version of it: “We’re going to unify Text Secure and Red Phone into Signal on Android, release a desktop version of Signal, and keep working to push the envelope of secure protocols and private communication,” said Marlinspike.
The accessibility of Signal 2.0 for iOS brings a measure of protection and secure correspondence that has been called for since the Quarks Lab report of 2013:
“Apple’s claim that they can’t read an end-to-end encrypted iMessage is definitely not true. As everyone suspected: yes they can! Suspecting does not know, and we hope to have dug enough in the protocol to show how Apple could do it. But shall we continue to use iMessage? MITM attacks on iMessage are unpractical to the average hacker and the privacy of iMessage is good enough for the average user. If the information’s being exchanged are sensitive to the point that you do not want any government agencies to look into them. Apple, make a more transparent PKI and document the protocol, and it could be considered the most practical and secure real-time messaging system available.”
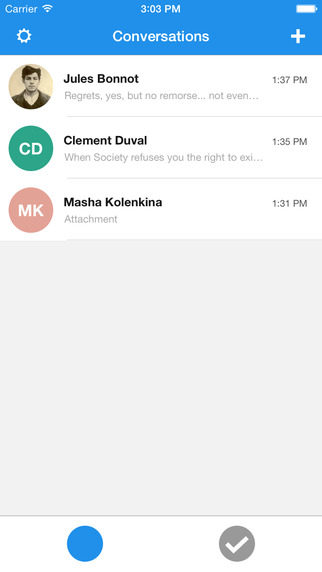
Image Source: iTunes – Screenshot of Signal 2.0 ‘Conversations’ space.
“It is technically possible that someone in control of Apple’s servers could intercept your communication,” Marlinspike said, adding that Signal 2.0 now permits iPhone clients to correspond secretly with clients on Android devices as well.
The convention behind Signal 2.0 is a unique one, one which basically creates a different encryption key for every message being sent, in this way if a key were to be cracked, not all messages would be exposed.
The process also permits clients to check one another’s individual encryption keys so that it would be simple to distinguish if an assailant was performing a ‘man in the middle’ attack, blocking activity between endpoints.
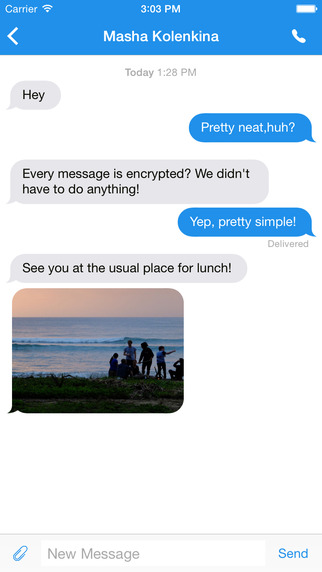
Image Source: iTunes – Screenshot of Signal 2.0 messaging interface.
The straightforwardness of Signal ought to uproot any hindrance for ‘protection cognizant’ users, as the application utilizes the mobile device’s current number and location, and does not require a different login or confirmation component to oversee. Clients have the capacity to send encrypted messages, pictures, videos and make encrypted calls worldwide, without any additional charges.
“We cannot hear your conversations or see your messages, and no one else can either. No exceptions. You can even tap and hold on a contact’s name to see advanced identity verification options. Everything in Signal is always end-to-end encrypted and painstakingly engineered in order to keep your communication safe.” -Signal 2.0 Product Description
If you are still not satisfied, you can always take a look at the source code available on GitHub, created by Open Whisper Systems.
AnonHQ recommends: Protect your PC & mobile devices from hackers and governments & surf and download anonymously
You want to support Anonymous Independent & Investigative News? Please, follow us on Twitter: Follow @AnonymousNewsHQ
SOURCES:
https://whispersystems.org/blog/the-new-signal/
https://itunes.apple.com/us/app/signal-private-messenger/id874139669?mt=8
http://thehackernews.com/2015/03/signal-encrypted-ios-text-calls.html





So what happens if some one hacks the Signal server? OMG, your screwed.
iMessage is just as secure as Signal. What can crack any communication system? Man in the middle. Who is in the middle of every internet transaction? NSA is. So nothing is truly safe other that you and the recipient being in the same room, no windows, using sign language. Even that can be busted using heat signatures to read you hand signals.
E2E encryption will encrypt the message on the device before sending it out. So “man in the middle” attacks won’t work unless Signal has the ability to decrypt messages. Court documents prove that Signal doesn’t hold they keys, just some very vague metadata.
William David, much shite, you do speak
Imessage has a key per conversation. Signal has key per MESSAGE!
Your messages DO NOT GO THROUGH signals servers!!! End to end, bell end!!
Signal, opensauce.
Imessage, closed sauce.
Apple has the key to your messages. Signal does not.
Signal does encrypted voice calling, imessage does not.
Signal is far superior, and that’s why its recommended by Ed Snowden… He knows what he’s talking about.