
If you found out that someone has been watching you the entire time how would you feel, reading every incoming-outbound messages from your cell phone and computer? This was not meant you scare you nevertheless, but millions of people feel the same way as you are right now. In June 2013 when a former National Security Agency contractor named Edward Snowden dropped the bomb on the agency and the government face – many people felt same about them being watched. Privacy fears aren’t limited to North America. During the summers of 2013 Research In Motion, a mother company of Blackberry gave away the tools to the Indian government to read the Blackberry messenger conversations. Likewise, Kakao Talk passed on the user messaging records to the Korean government following the lawful orders to take action, which led numerous customers to switch to Kakao Talk.
These types of changes have generated a surge of texting app providers that claim their software cannot be hacked. They state they utilize unique privacy technologies to guarantee the security of one’s data and prevent interception. Many say they incorporate industry-acknowledged security programs and open standard protocols for the overall safety of instant messages. Such security networks range from standard level to military grade. The traditional security technique is end-to-end encryption. And the way it works makes it unique. To put it simply – the information or your content gets locked in with unique value that is as soon as it leaves the sender’s cellphone or tablet – and it only gets unencrypted once the intended person receives it with verification that follows. These sophisticated privacy methods help prevent the most common workarounds for cracking the encoded information when in transit.
But, do not lose your confidence in online messaging tools yet. If you want to carry on chats minus anybody snooping, give consideration to trying out the following secure messaging applications listed below:-
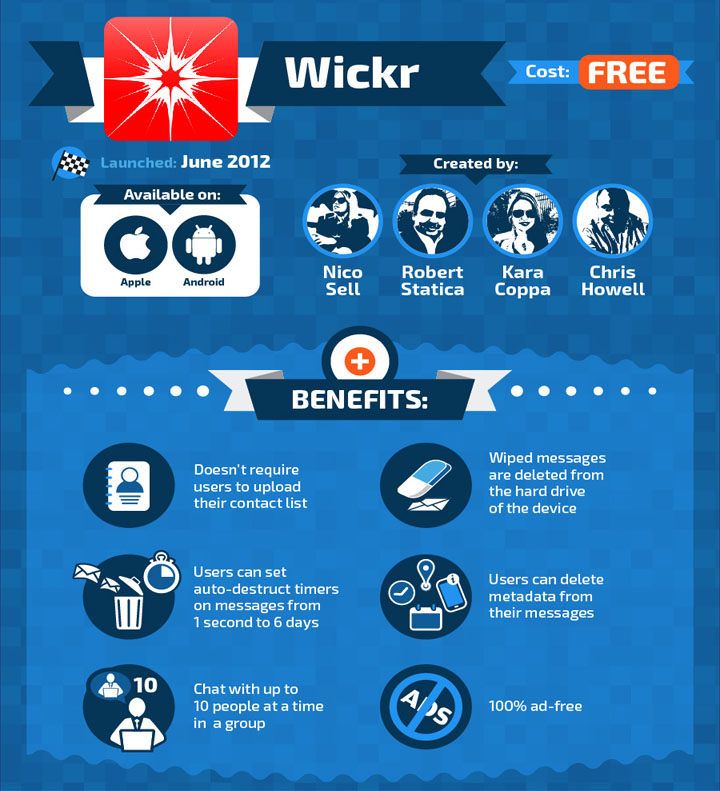
1) Wickr
This spot-on messenger for iOS and Android enable users to exchange end-to-end encrypted plus messages that can delete themselves (given the timeframe), including photos and files. It was made to ensure encryption and privacy and keeping the transparency for its users and keeps no data to its servers, plus it doesn’t maintain any information on its clients, and that all messages and transactions are encoded with no way to decrypt them.
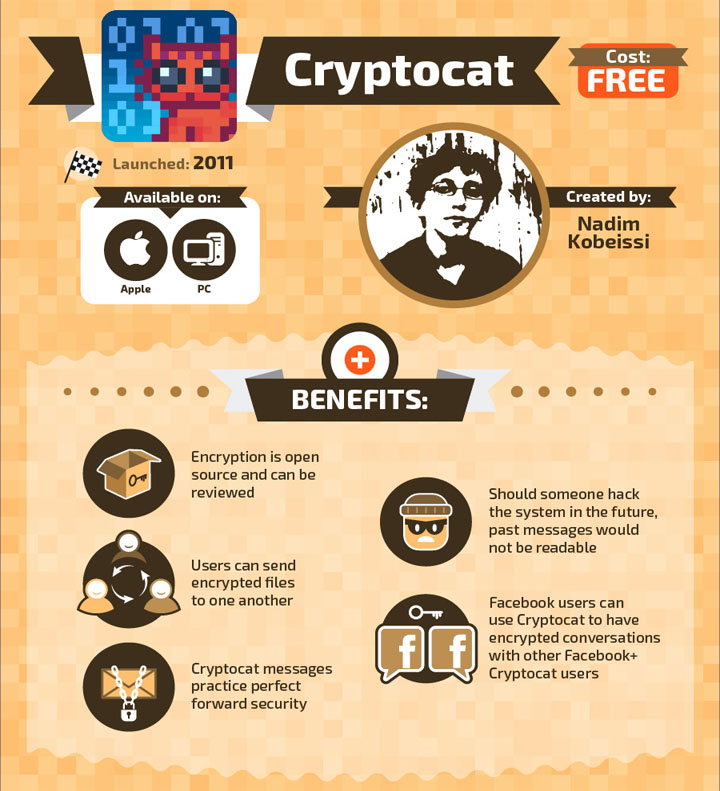
2) Cryptocat
Available for iPhone the software uses the Off-the-Record Messaging (OTR) protocol for protecting personal texting, allowing two people to converse in private. Cryptocat always utilizes its special team messaging protocol to allow for group instant messaging interactions. Because Cryptocat produces new key sets for every chat(s), it implements a form of best forward privacy. The application also offers protected file and photo transfer, letting users send documents and images to each other using end-to-end encryption.
Furthermore, they also provide internet browser extensions. Cryptocat is currently compatible with Google Chrome, Mozilla Firefox, Apple Safari, Opera and also offers a program for iOS devices.
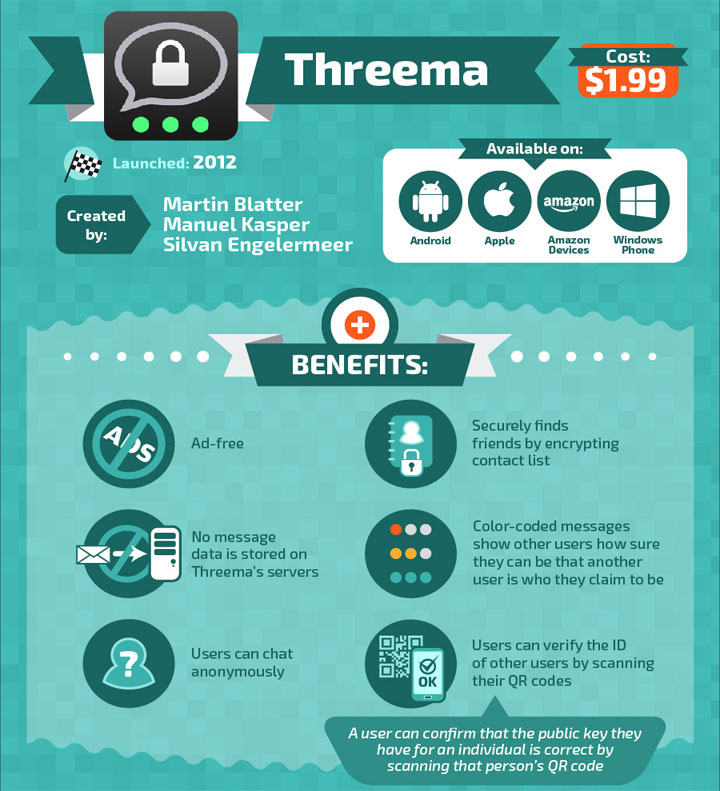
3) Threema
Available on iOS, Andriod & Windows this paid application employs a user ID, created once the application is launched by the user (they key is always random). However, instead than requiring a connected email or a personal number to send messages a person can provide the random key to the individual they wish to speak with. One can also find out may users by utilizing their phone book. Users can dispatch messages, images, videos, allow their location to be shown, send voice messages and send any type of file up to a max of twenty megabytes every single transfer. There is a function of creating polls in the group chats that can be used for business purposes.
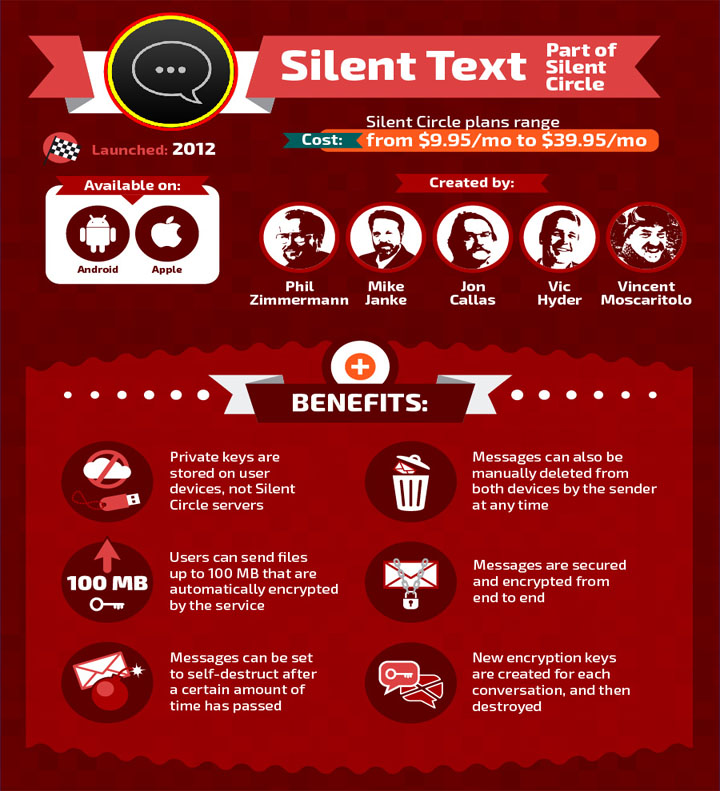
4) Silent Text
Available on both the iOS & Andriod this app comes with in-app purchases ranging from $9.95 a month to $39.95 the software has received points for having communications protected while they are still in transit, getting messages encrypted, making it possible for customers to verify their correspondent’s identity independently also making past interactions safe, if the key or the password is hacked.
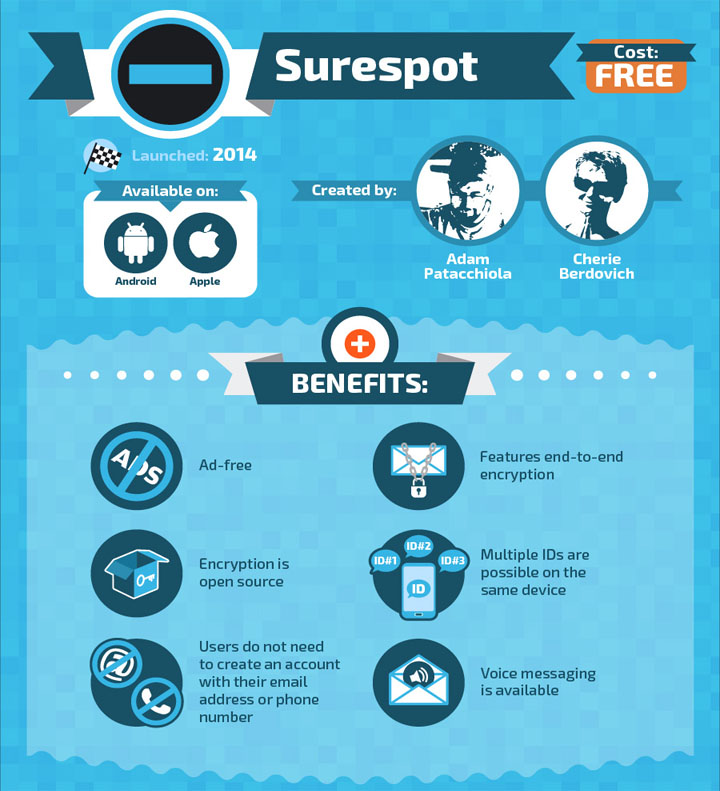
5) Surespot
Surespot is an instant messaging software for Android and iOS platforms which also uses end-to-end security layer by default. It removes any form of messages from the device if the recipient intends it to be that way. Much like TOR browser the app also offers multiple identities that can be switched at any given time. Unlike some software that were not mentioned on this list but are available on the market, it also supports sending and receiving pictures, as well as audio messages.
Getting to the point, Surespot runs on 256-bit AES-GCM encryption using keys created with 521 bit ECDH coding.
Source: Who Is Hosting This
You want to support Anonymous Independent & Investigative News? Please, follow us on Twitter: Follow @AnonymousNewsHQ
This Article (Top 5 Encrypted Messaging Apps For Your Device) is free and open source. You have permission to republish this article under a Creative Commons license with attribution to the author and AnonHQ.com.





What about TextSecure by OpenWhisper?
I too would like to hear your comment on these two.
Given the fact that Edward Snowden uses it, as mentioned in his Twitter account; I wouldn’t hesitate to use it.
What abt Telegram.org, is not good?
No , is not good , they request your phone number , so is same shit like normal call or chat 🙂
That has nothing to do with it. They request your phone number so they can know which devices have encryption abilities so they can auto encrypt when two users who support the feature attempt to communicate with each other. The same with texting.
Nevermind that, what is that logo on her phone?
The problem I have is most people around me don’t care and these platforms are only end to end encrypted with the same app. With so many apps it’s difficult to sell people. It’d be good if all apps on all platforms were end to end encryped – I could have a chance selling that to people.
Half the so-called safe messaging systems employee base have been either been infiltrated by government agencies or are in fact government agencies obviously…